- Updated: January 30, 2026
- 6 min read
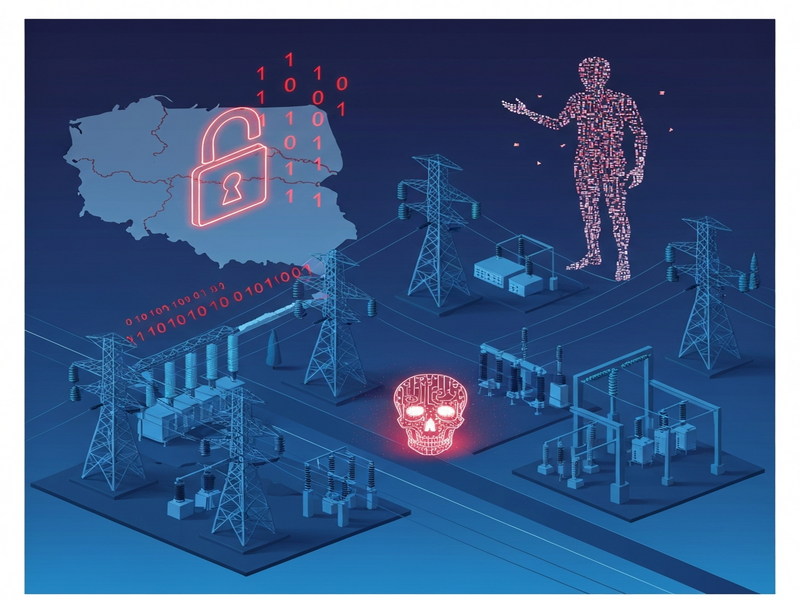
Russian Hackers’ Wiper Malware Attack Thwarts Poland Power Outage
The attempted cyber‑attack on Poland’s power grid in late December 2025 was successfully blocked; Russian‑linked Sandworm hackers deployed the destructive DynoWiper malware, but robust cybersecurity defenses prevented any outage.
What happened on Poland’s power grid?
On December 29‑30, 2025, Polish authorities detected a coordinated intrusion targeting two heat‑and‑power plants and the communication links that connect renewable installations such as wind farms to the national distribution network. The attack was described by Energy Minister Miloš Motyka as “the strongest assault on Poland’s energy infrastructure in years.”
According to a TechCrunch article, the perpetrators were identified as a Russian government‑backed group, widely known as Sandworm, which has a history of targeting critical infrastructure across Eastern Europe.
Who are the Russian‑backed hacking groups behind the attack?
Sandworm operates under Russia’s Main Directorate (GRU) and has been linked to several high‑profile cyber‑espionage and sabotage campaigns since at least 2014. Their signature tactics include:
- Deploying wiper malware that permanently erases data.
- Targeting supervisory control and data acquisition (SCADA) systems.
- Leveraging zero‑day exploits to bypass air‑gapped networks.
Sandworm’s most infamous operation was the 2015 and 2016 attacks on Ukraine’s power grid, which caused blackouts for hundreds of thousands of residents. The group’s continued focus on energy systems reflects a strategic aim to destabilize neighboring nations without crossing the threshold of kinetic warfare.
How the DynoWiper malware was used
Security firm ESET obtained a sample of the malicious payload, naming it DynoWiper. This wiper is designed to:
- Overwrite critical system files on Windows‑based industrial controllers.
- Delete backup images to make recovery impossible without external intervention.
- Trigger a cascade of system reboots, effectively taking the targeted plant offline.
Analysis showed a “medium confidence” attribution to Sandworm because DynoWiper shares code fragments with the Industroyer2 family, previously used against Ukrainian utilities. The malware also employed a custom command‑and‑control (C2) channel that leveraged Telegram bots for covert communications—a technique highlighted in the ChatGPT and Telegram integration documentation.
Official reactions and expert analysis
“Our detection systems flagged the intrusion within minutes, and our incident response team isolated the affected segments before any damage could spread,” said Deputy Minister of Digital Affairs Agnieszka Kowalska.
Cybersecurity researcher Kim Zetter, who first reported the incident, emphasized that the timing—just before the holiday season—mirrored previous Sandworm campaigns aimed at exploiting reduced staffing levels.
Poland’s Prime Minister Donald Tusk added, “Our critical infrastructure remained secure thanks to the vigilance of our operators and the resilience of our cyber‑defence architecture.”
Why the power grid stayed online
Several layers of protection contributed to the successful mitigation:
- Real‑time anomaly detection: Advanced SIEM solutions flagged abnormal traffic to the SCADA network.
- Network segmentation: Critical control systems were isolated from corporate IT, limiting lateral movement.
- AI‑driven threat hunting: Operators employed AI platforms such as the UBOS platform overview to automatically correlate logs and generate actionable alerts.
- Incident response playbooks: Pre‑written runbooks enabled rapid containment and forensic data collection.
These measures prevented the malware from reaching the core PLCs (Programmable Logic Controllers) that manage turbine output, thereby averting a potential blackout for an estimated half‑million households.
Lessons from Ukraine’s 2015‑2016 power outages
When Sandworm struck Ukraine, the attackers succeeded in disabling backup generators and causing prolonged outages. The key differences this time are:
| Aspect | Ukraine (2015‑16) | Poland (2025) |
|---|---|---|
| Malware type | Industroyer2 (wiper) | DynoWiper (wiper) |
| Detection speed | Hours to days | Minutes |
| Network segmentation | Limited | Robust, air‑gapped |
| Outcome | Power loss for 230k+ homes | No outage, systems remained operational |
The Polish experience demonstrates how modern security architectures, combined with AI‑enhanced monitoring, can neutralize threats that previously caused widespread disruption.
Why resilient cybersecurity matters for energy grids
Critical infrastructure is increasingly a target for state‑sponsored cyber‑operations. The stakes are high:
- Economic impact – a single hour of outage can cost millions of euros.
- Public safety – loss of heating in winter endangers vulnerable populations.
- Geopolitical leverage – cyber‑attacks can be used as coercive tools without crossing a kinetic threshold.
Adopting a layered defense model—often called “defense in depth”—is essential. Modern AI platforms can automate many of these layers, from threat intelligence ingestion to automated patch management.
AI tools that can fortify power‑grid defenses
UBOS offers a suite of AI‑driven services that help utilities stay ahead of sophisticated adversaries:
- AI marketing agents – while primarily for outreach, the underlying language models can be repurposed for threat‑intel summarization.
- Workflow automation studio – automates incident‑response playbooks, reducing mean‑time‑to‑contain.
- UBOS templates for quick start – includes pre‑built security monitoring dashboards.
- OpenAI ChatGPT integration – enables natural‑language querying of log data for faster investigations.
- Chroma DB integration – provides vector‑based similarity search across threat‑intel feeds.
- ElevenLabs AI voice integration – can broadcast real‑time alerts to on‑call engineers via voice assistants.
For example, the AI SEO Analyzer template demonstrates how large‑scale text analysis can be repurposed to sift through thousands of security advisories daily, surfacing the most relevant CVEs for grid operators.
What’s next for Poland and the broader energy sector?
Poland’s successful defense is a proof point, but the threat landscape will only intensify. Experts recommend the following actions:
- Continuous red‑team testing: Simulate wiper attacks to validate detection and response capabilities.
- Zero‑trust network architecture: Enforce strict identity verification for every device and user.
- AI‑augmented SOCs: Deploy platforms like the Enterprise AI platform by UBOS to correlate telemetry at scale.
- Supply‑chain hardening: Vet third‑party software and firmware for hidden backdoors.
- Regulatory collaboration: Share indicators of compromise (IOCs) across EU member states via CERT‑EU.
By integrating these measures, utilities can transform reactive defense into proactive resilience, ensuring that even the most sophisticated state actors cannot easily disrupt power delivery.
How you can strengthen your organization’s cyber posture
If you’re an IT security professional or energy‑sector manager, consider exploring UBOS’s UBOS pricing plans to find a solution that fits your budget. Start with a free trial of the Web app editor on UBOS to prototype custom monitoring dashboards without writing code.
For startups looking to embed AI quickly, the UBOS for startups program offers mentorship and discounted access to the full suite of AI tools.
Stay ahead of emerging threats—subscribe to our newsletter, explore the UBOS portfolio examples, and join the UBOS partner program to collaborate on next‑generation cybersecurity solutions.
