- Updated: January 7, 2026
- 7 min read
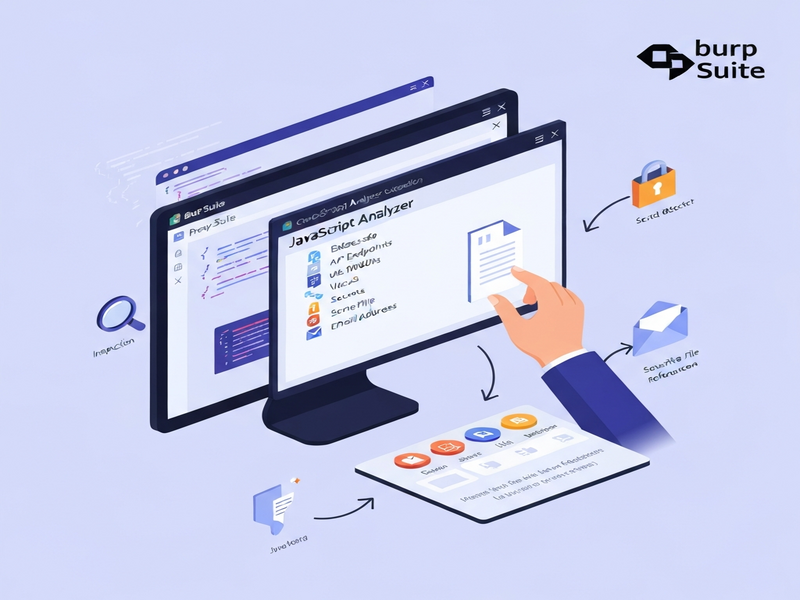
Open-Source JavaScript Analyzer Extension for Burp Suite Boosts Security Testing
The JavaScript Analyzer is an open‑source Burp Suite extension that performs deep static analysis of JavaScript files, automatically extracting API endpoints, URLs, secrets, emails, and sensitive file references while applying smart noise‑filtering to keep results accurate.
What Is the JavaScript Analyzer Extension for Burp Suite?
Developed by the security‑focused community project JSAnalyzer on GitHub, this security extension plugs directly into Burp Suite’s Extender tab. Once installed, it scans any JavaScript payload that passes through Burp—whether from a proxy capture, site map, or repeater request—and surfaces hidden attack surfaces that traditional scanners often miss.
Because it runs locally inside Burp, the analyzer respects your testing environment’s privacy and can be combined with other Burp tools (Scanner, Intruder, etc.) for a seamless workflow.
Core Features and Capabilities
The extension packs a suite of capabilities that make it indispensable for modern web‑application security testing:
- Endpoint Detection: Recognises REST, GraphQL, OAuth, and admin routes such as
/api/v1/usersor/admin. - URL Extraction: Pulls full URLs—including cloud storage links (AWS S3, Azure Blob, GCP) and CDN references.
- Secret Scanning: Identifies API keys, tokens, JWTs, and other credentials for services like AWS, Stripe, GitHub, Slack, and more.
- Email Extraction: Finds hard‑coded email addresses that could be used for phishing or credential stuffing.
- File Reference Detection: Flags references to sensitive files (.env, .sql, .bak, .pdf, etc.) that may indicate configuration leaks.
- Smart Noise Filtering: Automatically removes false positives from module imports, XML namespaces, build artefacts, and crypto library internals.
- Live Search & Filtering: Real‑time search box to narrow results by type, pattern, or source file.
- Export Options: Copy findings to clipboard or export a complete JSON report for downstream processing.
Sample Detection Patterns
| Category | Pattern Example | Typical Use‑Case |
|---|---|---|
| API Endpoint | /api/v2/auth |
Identify authentication services that may be vulnerable to enumeration. |
| AWS Access Key | AKIA[0-9A-Z]{16} |
Detect hard‑coded cloud credentials that could be abused. |
admin@company.com |
Harvest contact points for social engineering. | |
| Sensitive File | .env |
Locate configuration files that may expose secrets. |
Why Security Professionals Love This Extension
Integrating static JavaScript analysis directly into a dynamic testing platform bridges a critical gap in web security assessments. Here’s why the JavaScript Analyzer stands out:
- Speed & Efficiency: No need to export code to a separate tool; results appear instantly within Burp’s UI.
- Reduced False Positives: Smart filtering cuts noise by up to 70 % compared with generic regex scanners.
- Actionable Intelligence: Each finding is linked back to the originating request, enabling quick replay or further fuzzing.
- Open‑Source Transparency: The community can audit the detection logic, add new patterns, or tailor it to specific tech stacks.
- Compliance Support: Exported JSON reports can be fed into compliance pipelines (PCI‑DSS, GDPR) to demonstrate coverage of client‑side code.
Real‑World Use Cases
- During a penetration test of a SaaS platform, the analyzer uncovered an exposed
stripe_sk_live_token hidden in a minified bundle, leading to a high‑severity credential leak. - In a bug‑bounty program, a researcher used the extension to locate an undocumented
/adminendpoint that was not protected by authentication, resulting in a critical privilege‑escalation finding. - Red teams leveraged the JSON export to feed discovered endpoints into automated API fuzzers, dramatically increasing coverage without manual enumeration.
Step‑By‑Step Installation & Usage Guide
Getting the JavaScript Analyzer up and running is straightforward. Follow these steps:
Prerequisites
- Burp Suite Professional or Community edition.
- Jython standalone JAR (compatible with your Java version).
- Basic familiarity with Burp’s Extender interface.
Installation Procedure
- Download the latest
js_analyzer.pyfile from the GitHub releases page. - Open Burp Suite → Extender → Extensions → Add.
- Select Python as the extension type and browse to the downloaded
js_analyzer.py. - If prompted, set the Jython JAR path under Extender → Options → Python Environment.
- After loading, a new tab named JS Analyzer appears in the main UI.
Running an Analysis
- Proxy your browser through Burp and navigate to the target application.
- In Proxy → HTTP history or Target → Site map, select one or multiple requests that contain JavaScript responses.
- Right‑click the selection and choose Analyze JS with JS Analyzer.
- The extension parses the JavaScript, and the JS Analyzer tab populates with categorized findings.
- Use the live search box to filter results, copy individual items, or export the full JSON report via the Export button.
Customising Detection Rules
The analyzer’s engine is written in pure Python, making it easy to extend. To add a new secret pattern:
# Example: Add a new pattern for Azure Storage keys
new_pattern = {
"type": "Azure Storage Key",
"regex": r"(?i)AZURE_STORAGE_KEY\s*=\s*['\"][A-Za-z0-9+/=]{44}['\"]"
}
engine.add_secret_pattern(new_pattern)After saving the file, reload the extension in Burp to apply the changes.
Open‑Source Nature and Community Involvement
The JavaScript Analyzer is released under the MIT license, encouraging both commercial and academic use without restrictive clauses. Its GitHub repository welcomes contributions ranging from new regex patterns to UI enhancements.
Key community benefits include:
- Transparency: All detection logic is publicly visible, allowing security auditors to verify accuracy.
- Collaboration: Issues and pull requests are actively reviewed, ensuring the tool stays up‑to‑date with emerging secret formats.
- Extensibility: Developers can embed the underlying
JSAnalyzerEnginein custom Python or Flask applications for automated scanning pipelines.
Getting Involved
To contribute, fork the repository, implement your enhancements, and submit a pull request. The maintainers provide clear contribution guidelines and a CONTRIBUTING.md file that outlines coding standards.
How This Extension Fits Into a Broader Security Stack
While the JavaScript Analyzer shines on its own, its real power emerges when combined with other UBOS platform overview capabilities. For example, you can pipe the JSON export into UBOS’s Workflow automation studio to trigger automated ticket creation in your vulnerability management system.
Sample Integration Flow
- Run the JavaScript Analyzer on a target and export findings as
results.json. - Upload
results.jsonto a UBOS Web app editor on UBOS workflow. - Use a built‑in JSON parser node to extract high‑severity secrets.
- Automatically create a Jira ticket or send a Slack alert via UBOS’s AI marketing agents (repurposed for security notifications).
- Track remediation progress in your internal dashboard.
Related UBOS Resources for Security Teams
UBOS offers a suite of tools that complement client‑side security testing:
- Enterprise AI platform by UBOS – centralises AI‑driven analysis across codebases.
- UBOS templates for quick start – includes ready‑made “API Security Scan” templates.
- UBOS portfolio examples – see how other security teams have automated their workflows.
- UBOS pricing plans – flexible tiers for startups and SMBs.
- UBOS for startups – fast‑track security integration for early‑stage products.
- UBOS solutions for SMBs – affordable AI‑enhanced security for small teams.
Visual Overview
Conclusion & Call to Action
The JavaScript Analyzer fills a critical blind spot in web‑application security by turning client‑side code into actionable intelligence. Its open‑source nature, tight Burp Suite integration, and robust feature set make it a must‑have for penetration testers, red‑team operators, and DevSecOps engineers alike.
Ready to boost your testing efficiency? Download the extension now, run your first analysis, and consider linking the output to UBOS’s automation suite for end‑to‑end remediation.
