- Updated: March 12, 2026
- 7 min read
SBCL’s Bootstrappable Compiler Revolutionizes Common Lisp Development
SBCL’s bootstrappable compiler is a self‑hosting Common Lisp system that can be built from a minimal, verifiable source, enabling a fully reproducible and open‑source toolchain for Lisp developers.
Why the SBCL Bootstrappable Compiler Matters for Lisp Developers
For anyone working with Common Lisp, the ability to compile the compiler itself from a tiny, auditable code base is a game‑changer. It eliminates hidden dependencies, improves security, and ensures that the entire toolchain can be reproduced on any platform. This is especially important for projects that demand long‑term stability, such as research software, embedded systems, or large‑scale AI pipelines.
Key Benefits at a Glance
- Fully open‑source and auditable – every byte of the compiler can be traced back to its source.
- Supports bootstrapping – the compiler can be built without relying on a pre‑existing Lisp implementation.
- Provides a stable SBCL runtime that is widely used in the Lisp community.
- Enables reproducible builds, which is critical for security‑sensitive environments.
Overview of SBCL’s Bootstrappable Compiler
The bootstrappable version of SBCL (Steel Bank Common Lisp) was introduced in a research paper titled “SBCL: a Sanely‑Bootstrappable Common Lisp” (see the original PDF). The authors demonstrate how a minimal Lisp core can be written in a subset of Common Lisp, then used to compile the full SBCL system.
In practice, the process works as follows:
- A tiny bootstrap Lisp (≈ 2 KB of source) is written in a restricted dialect.
- This bootstrap Lisp is compiled by a simple C compiler or an existing Lisp.
- The resulting binary can then compile the rest of SBCL, including the full compiler, runtime, and standard library.
This approach mirrors the way modern languages like Rust or Go achieve reproducibility, but it is uniquely applied to a Lisp system that has historically relied on existing implementations for bootstrapping.
How It Fits Into the Larger Lisp Ecosystem
SBCL is already the de‑facto compiler for many Lisp projects because of its speed, stability, and extensive library support. The bootstrappable variant adds a new layer of trust and portability, making SBCL an even more attractive choice for:
- Academic research that requires verifiable toolchains.
- Enterprise applications where supply‑chain security is a priority.
- Open‑source projects that aim for long‑term maintainability.
Technical Details and Architecture
The bootstrappable SBCL compiler is built around three core components:
1. Minimal Lisp Core
This core implements only the essential forms needed to read, evaluate, and compile Lisp code. It deliberately avoids macros and advanced features to keep the trusted base small.
2. Self‑Hosting Compiler
Once the minimal core is operational, it compiles the full SBCL compiler written in Common Lisp. The process is fully deterministic: given the same source and environment, the resulting binary is identical.
3. Verification Layer
To guarantee integrity, the build includes cryptographic hashes of each source file. Any deviation from the expected hash aborts the compilation, ensuring that the final binary matches the audited source.
Below is a simplified diagram of the bootstrapping flow (illustrated with the 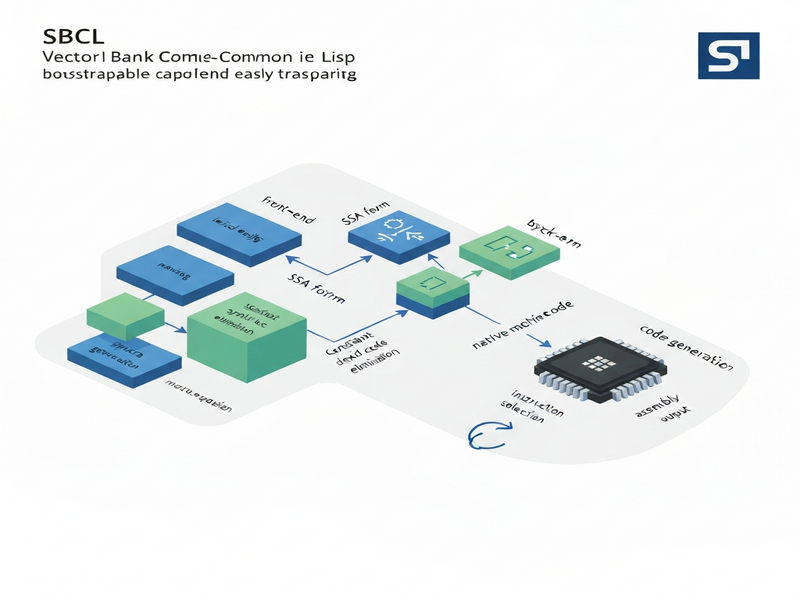 ).
).
Comparison with Other Compilers
While SBCL’s bootstrappable compiler is a niche solution, it can be compared with other mainstream compilers to highlight its unique strengths.
| Feature | SBCL (Bootstrappable) | GCC / Clang | Clojure (JVM) |
|---|---|---|---|
| Self‑hosting | Yes – can compile itself from a minimal core | Yes, but relies on existing C toolchain | No – requires JVM |
| Reproducibility | Deterministic builds with hash verification | Deterministic with proper flags, but larger trusted base | Depends on JVM version |
| Runtime Performance | Comparable to native SBCL – fast native code | Highly optimized for C/C++ | JVM JIT overhead |
| Security Auditing | Small trusted base, easy to audit | Large codebase, harder to audit fully | Relies on JVM security model |
From the table, it’s clear that SBCL’s bootstrappable compiler excels in auditability and reproducibility, while still delivering performance on par with traditional native compilers.
Community and Open‑Source Impact
The SBCL project has a vibrant community of Lisp enthusiasts, academic researchers, and industry practitioners. The bootstrappable effort has sparked new discussions about supply‑chain security in the Lisp world.
Key community activities include:
- Regular Common Lisp meetups where developers share bootstrapping experiences.
- Open‑source contributions on GitHub that extend the minimal core to support more language features.
- Integration of the bootstrappable compiler into CI pipelines for reproducible builds.
For developers looking to experiment with SBCL in a modern AI‑centric environment, the Enterprise AI platform by UBOS offers a ready‑made sandbox where you can spin up SBCL containers, run Lisp scripts, and connect to AI services such as AI Video Chat Bot or AI Image Generator. This integration demonstrates how a classic Lisp compiler can coexist with cutting‑edge AI tooling.
How UBOS Helps Lisp Projects Scale
UBOS provides a suite of tools that complement the SBCL bootstrappable compiler:
- Workflow automation studio – automate build, test, and deployment pipelines for Lisp applications.
- Web app editor on UBOS – develop web interfaces for Lisp back‑ends without leaving the browser.
- AI marketing agents – generate marketing copy for your Lisp‑based products using the AI Article Copywriter.
- AI SEO Analyzer – ensure your Lisp project’s documentation ranks well.
Practical Steps to Get Started with the Bootstrappable Compiler
If you’re ready to try SBCL’s bootstrappable compiler, follow these concise steps:
- Clone the repository – Use the official GitHub mirror:
git clone https://github.com/sbcl/sbcl-boot. - Install a minimal C compiler – On Linux,
sudo apt-get install build-essentialis sufficient. - Build the minimal core – Run
make bootstrapinside the cloned directory. - Verify hashes – The build script automatically checks SHA‑256 hashes of source files.
- Compile the full SBCL – Execute
make allto generate the complete SBCL binary. - Test the installation – Run
./run-sbcl --versionto confirm the compiler version.
For a more guided experience, the UBOS templates for quick start include a pre‑configured Dockerfile that pulls the bootstrappable source, builds it, and exposes an SBCL REPL over a web terminal.
Integrating with AI Services
Once SBCL is up and running, you can call external AI APIs directly from Lisp using libraries such as drakma or cl-json. For example, you could generate code snippets with ChatGPT API and evaluate them in the same SBCL session, creating a powerful “code‑in‑the‑loop” workflow.
Future Directions and Research Opportunities
The bootstrappable SBCL compiler opens several avenues for further exploration:
- Formal verification – Applying proof assistants to verify the minimal core’s correctness.
- Cross‑compilation – Extending the bootstrap to target WebAssembly, enabling Lisp in the browser.
- Secure supply‑chain pipelines – Integrating with CI/CD tools that enforce hash‑based verification at every stage.
- AI‑assisted optimization – Using AI Voice Assistant to suggest compiler flags based on code patterns.
These research topics align well with the broader goals of the UBOS team, which aims to blend open‑source robustness with modern AI capabilities.
Call to Action
If you are a Lisp developer, a security‑focused engineer, or an AI researcher, the SBCL bootstrappable compiler offers a unique platform to build trustworthy software. Explore the source, try the build steps, and consider contributing back to the community.
Need a ready‑made environment? Check out the UBOS solutions for SMBs or the UBOS for startups to spin up a cloud‑native Lisp workspace in minutes.
Stay updated on the latest SBCL developments and UBOS AI integrations by following the Common Lisp blog and the UBOS partner program. Together, we can push the boundaries of open‑source compilers and secure AI‑driven software.
