- Updated: February 16, 2026
- 6 min read
Harnessing PostgreSQL Race Conditions with Synchronization Barriers – A Comprehensive Guide
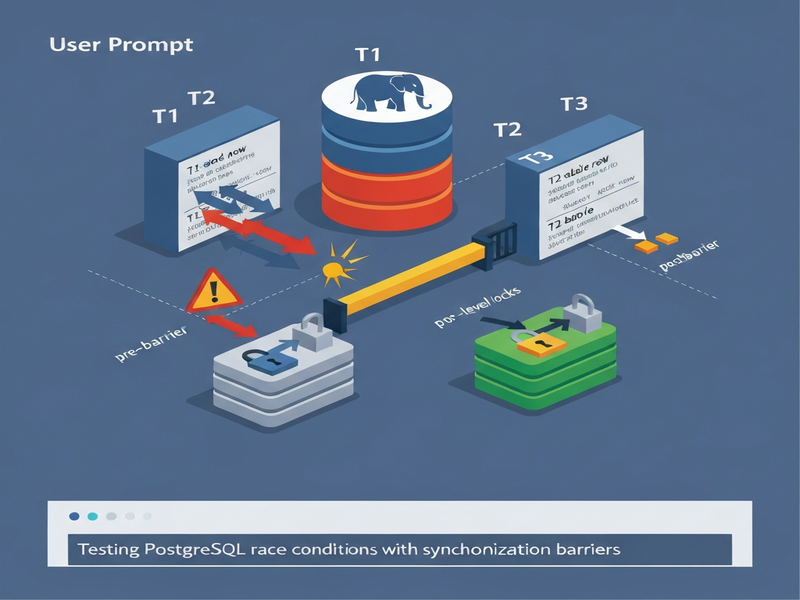
PostgreSQL race conditions occur when two or more concurrent transactions read the same row, compute new values based on that stale data, and then overwrite each other’s updates, resulting in lost or incorrect data.
Why PostgreSQL Race Conditions Matter for Modern Apps
In high‑throughput services—payment gateways, inventory systems, or real‑time analytics—every millisecond counts. A hidden race condition can silently corrupt financial balances or inventory counts, and the bug may never surface until it hits production. The recent deep‑dive by LIR Bank explains how harnessing PostgreSQL race conditions can turn a silent failure into a reproducible test case.
This article walks you through the nature of these bugs, why traditional unit tests miss them, and how synchronization barriers give you deterministic control over concurrency. Whether you’re a DBA, backend engineer, or DevOps specialist, you’ll walk away with a concrete testing methodology you can plug into any CI pipeline.
What Are PostgreSQL Race Conditions?
A race condition in PostgreSQL is a classic lost‑update problem. Two transactions execute the following steps in parallel:
- Read the current value of a row (e.g., an account balance).
- Compute a new value based on the read data.
- Write the new value back to the same row.
If both transactions read the same original value before either writes, the second write overwrites the first, leaving the database in an inconsistent state. The following code snippet illustrates the problem in JavaScript‑style pseudo‑code:
// Two concurrent credits
SELECT balance FROM accounts WHERE id = 1; // both return 100
-- compute new balance
UPDATE accounts SET balance = 150 WHERE id = 1; // both write 150
-- final balance is 150, not 200PostgreSQL faithfully executes each statement, so no error is raised. The bug lives in the application logic, not the database engine.
Key takeaway: Without explicit locking or higher isolation levels, concurrent writes can silently lose data. Detecting this requires a test that forces the exact interleaving described above.
How Synchronization Barriers Turn Flaky Bugs into Deterministic Tests
A barrier is a simple coordination primitive: each concurrent task signals its arrival and then waits until all expected tasks have arrived. Once the last task reaches the barrier, all are released simultaneously. This guarantees that every transaction reaches the same point in its execution before proceeding.
By inserting a barrier between the SELECT and the UPDATE, you force both transactions to read the stale value before either writes. The result is a reproducible lost‑update scenario—no timing tricks, no flaky sleeps.
function createBarrier(count) {
let arrived = 0;
const waiters = [];
return async () => {
arrived++;
if (arrived === count) {
waiters.forEach(resolve => resolve());
} else {
await new Promise(res => waiters.push(res));
}
};
}The barrier itself lives only in test code; production code remains untouched. This separation is crucial for performance and security, and it aligns with the About UBOS philosophy of clean, modular architecture.
Step‑by‑Step: Building a Reliable PostgreSQL Race‑Condition Test Suite
1. Prepare a Real PostgreSQL Instance
Mock databases cannot emulate row‑level locks or transaction isolation. Spin up a disposable instance using Docker, Neon, or any cloud‑native service. UBOS makes this painless with its UBOS platform overview, which includes one‑click PostgreSQL provisioning.
2. Implement the Barrier Helper
Add the createBarrier function to your test utilities. Keep it in a separate module so production code never imports it.
3. Refactor the Business Logic to Accept Hooks
Introduce an optional hooks argument that fires at the exact point you want to pause. Example:
async function credit(accountId, amount, hooks) {
await db.transaction(async tx => {
if (hooks?.onRead) await hooks.onRead(); // barrier injected here
const [{ balance }] = await tx.query(
`SELECT balance FROM accounts WHERE id = $1 FOR UPDATE`, [accountId]
);
const newBalance = balance + amount;
await tx.query(
`UPDATE accounts SET balance = $1 WHERE id = $2`, [newBalance, accountId]
);
});
}4. Write the Barrier‑Enabled Test
In your test file, create a barrier for two concurrent calls and invoke the function twice:
const barrier = createBarrier(2);
await Promise.all([
credit(1, 50, { onRead: barrier }),
credit(1, 50, { onRead: barrier })
]);
const [{ balance }] = await db.query(`SELECT balance FROM accounts WHERE id = 1`);
expect(balance).toBe(200); // will fail if lock is missing5. Verify Both Directions
Run the test with the FOR UPDATE lock enabled— it should pass. Then remove the lock and confirm the test fails. This double‑check guarantees the test is not a “vanity” test.
6. Integrate Into CI/CD
Because the test is deterministic, you can safely add it to your CI pipeline. If the test ever fails, the pipeline stops, preventing a regression from reaching production.
“A barrier test that passes with a lock and fails without it is the gold standard for concurrency safety.” – UBOS portfolio examples
Benefits & Best Practices for PostgreSQL Database Testing
- Deterministic failures: No more flaky sleeps or random retries.
- Early detection: Race conditions are caught during development, not after a costly production incident.
- Documentation of intent: The barrier code serves as living documentation of where concurrency matters.
- Scalable to many scenarios: The same pattern works for inventory decrements, token bucket rate limiting, and any read‑modify‑write workflow.
Best‑Practice Checklist
- Always run tests against a real PostgreSQL instance (PostgreSQL guide).
- Use
SELECT … FOR UPDATEor higher isolation levels (SERIALIZABLE) where appropriate. - Keep barrier helpers isolated from production code.
- Document the expected concurrency model in your API contracts.
- Combine barrier tests with load‑testing tools (e.g., Workflow automation studio) to simulate real traffic.
For teams looking to accelerate the creation of such tests, UBOS offers ready‑made templates. The UBOS templates for quick start include a “Database Concurrency Test” starter that wires the barrier logic into a CI‑ready workflow.
Moreover, if you need to surface insights from test runs—like identifying hot rows or lock contention—pair the tests with the AI marketing agents or the Web app editor on UBOS to build dashboards that alert you in real time.
Conclusion: Make Race Conditions a Non‑Issue
PostgreSQL race conditions are silent killers, but with synchronization barriers you can turn them into deterministic, testable scenarios. By embedding barrier‑enabled tests into your CI pipeline, you protect your data integrity, reduce downtime, and gain confidence that every refactor preserves correctness.
Ready to future‑proof your database layer? Explore the UBOS pricing plans for a free tier, spin up a PostgreSQL sandbox, and start building barrier tests today. For startups, the UBOS for startups program offers dedicated support and pre‑built templates.
Join the UBOS partner program to collaborate with other engineers who are already mastering concurrency testing. Together, we can make lost updates a thing of the past.
