- Updated: March 15, 2026
- 8 min read
Deterministic TCP Hole Punching: A Comprehensive Guide
TCP hole punching is a NAT‑traversal technique that lets two hosts located behind separate NAT routers create a direct TCP connection without relying on a relay server, by synchronizing port selection and timing through a deterministic algorithm.
Deterministic TCP Hole Punching: A Complete Guide for Network Engineers
Why deterministic TCP hole punching matters
Traditional NAT traversal often depends on external services such as STUN, TURN, or custom signaling channels. While effective, these solutions add latency, cost, and operational complexity. A deterministic approach eliminates the need for any third‑party coordination by deriving all required metadata—from timestamps to port numbers—using a shared mathematical model. This makes testing, debugging, and even production deployments simpler, especially for peer‑to‑peer (P2P) applications where low latency is critical.
For teams building real‑time gaming, VoIP, or IoT communication stacks, understanding the inner workings of this algorithm can reduce reliance on cloud‑based relay services and improve overall network efficiency. The UBOS platform overview already showcases how deterministic networking can be embedded into low‑code solutions, giving developers a head start.
The Deterministic Algorithm in Detail
1️⃣ Bucket selection – synchronizing “now” without communication
Both peers start with a shared time window derived from the Unix timestamp. Because network clocks drift, the algorithm defines a max_clock_error (commonly 20 seconds) and a min_run_window (e.g., 10 seconds). The calculation looks like this:
now = timestamp()
max_clock_error = 20
min_run_window = 10
window = (max_clock_error * 2) + 2
bucket = int((now - max_clock_error) // window)The resulting bucket is an integer that both sides can compute independently, guaranteeing that they operate within the same temporal slice even if their clocks differ by a few seconds.
2️⃣ Port generation – turning the bucket into a reproducible port list
NAT devices often preserve the source port when creating an external mapping (known as “equal‑delta mapping”). By seeding a pseudo‑random number generator (PRNG) with the bucket, each peer can independently produce an identical list of candidate ports.
large_prime = 2654435761
stable_boundary = (bucket * large_prime) % 0xFFFFFFFF
ports = [randrange(1024, 65535) for _ in range(16)]The algorithm discards any port that the operating system refuses to bind, ensuring that the final list contains only usable values. This deterministic port set eliminates the need for an exchange of port predictions via a signaling server.
3️⃣ Socket setup – configuring non‑blocking sockets for aggressive SYN bursts
Successful TCP hole punching hinges on precise timing. Each peer creates a non‑blocking socket with the following options:
SO_REUSEADDR– allows the same local address to be bound multiple times.SO_REUSEPORT– enables multiple sockets to listen on the same port, a prerequisite for rapid SYN retransmission.
Using select() (or its modern equivalents) the application polls for write readiness and repeatedly calls connect_ex() on each (dest_ip, port) pair, sleeping only a few milliseconds between attempts. This “burst” approach maximizes the chance that both NATs create matching external mappings before the OS transitions the socket into TIME_WAIT.
4️⃣ Winner selection – agreeing on a single successful connection
Because multiple ports may succeed simultaneously, the peers need a deterministic way to pick the same connection. The algorithm designates the host with the higher public IP as the leader. The leader sends a single byte (e.g., $) on each successful socket and immediately closes all others. The follower monitors its sockets; the one that receives the byte becomes the winner.
This single‑byte handshake is atomic and avoids the need for complex stream parsing, keeping the protocol lightweight and robust against packet reordering.
Putting It All Together: A Minimal Working Example
Below is a high‑level overview of a Python script (tcp_punch.py) that implements the deterministic algorithm. The code is intentionally concise to illustrate the core steps without overwhelming the reader.
import socket, selectors, time, random, struct
# 1️⃣ Compute bucket
now = int(time.time())
max_err = 20
window = (max_err * 2) + 2
bucket = (now - max_err) // window
# 2️⃣ Derive ports
prime = 2654435761
seed = (bucket * prime) & 0xFFFFFFFF
random.seed(seed)
ports = [random.randint(1024, 65535) for _ in range(16)]
# 3️⃣ Create non‑blocking sockets
sel = selectors.DefaultSelector()
sockets = []
for p in ports:
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.setsockopt(socket.SOL_SOCKET, socket.SO_REUSEADDR, 1)
s.setsockopt(socket.SOL_SOCKET, socket.SO_REUSEPORT, 1)
s.setblocking(False)
try:
s.bind(('', p))
sockets.append(s)
sel.register(s, selectors.EVENT_WRITE)
except OSError:
continue
# 4️⃣ Aggressive SYN burst
target_ip = "203.0.113.45" # remote public IP
deadline = time.time() + 10 # 10‑second window
while time.time() socket.gethostbyname(socket.gethostname()):
key.fileobj.send(b"$")
# close all others
for other in sockets:
if other is not key.fileobj:
other.shutdown(socket.SHUT_RDWR)
other.close()
break
The script demonstrates how the bucket, port list, and socket options combine to achieve a deterministic TCP hole punch. In a real deployment you would replace the hard‑coded target_ip with the remote peer’s public address obtained via a lightweight signaling channel (e.g., a short‑lived WebSocket or MQTT message).
For developers who prefer a visual, low‑code environment, the Web app editor on UBOS can generate similar socket logic using drag‑and‑drop components, accelerating prototyping for P2P services.
Benefits & Real‑World Use Cases
Deterministic TCP hole punching offers several tangible advantages over conventional NAT traversal methods:
- No persistent relay costs: By removing TURN servers, operational expenses drop dramatically.
- Lower latency: Direct TCP paths avoid the extra hop through a relay, which is crucial for real‑time gaming and voice communication.
- Predictable firewall behavior: Since the same ports are used on both ends, firewall rules can be pre‑configured, simplifying compliance for enterprise environments.
- Scalable P2P networks: Each new peer can join without provisioning additional server capacity.
Key Application Domains
- Online multiplayer gaming: Fast, low‑latency connections improve player experience. The deterministic approach can be embedded into game servers using the Enterprise AI platform by UBOS for matchmaking analytics.
- Voice over IP (VoIP) and video conferencing: Direct TCP streams reduce jitter and packet loss, especially in bandwidth‑constrained environments.
- IoT device coordination: Sensors and actuators often sit behind NATs; deterministic hole punching enables secure, peer‑to‑peer firmware updates without cloud brokers.
- File‑sharing and decentralized storage: Projects like IPFS benefit from deterministic port selection to improve peer discovery reliability.
- Secure remote administration: System administrators can establish direct, encrypted TCP tunnels without exposing management ports to the internet.
Companies leveraging AI‑driven automation can combine deterministic networking with AI marketing agents to trigger real‑time notifications when a new peer joins a network, creating dynamic, context‑aware campaigns.
Illustration of the Deterministic TCP Hole‑Punching Process
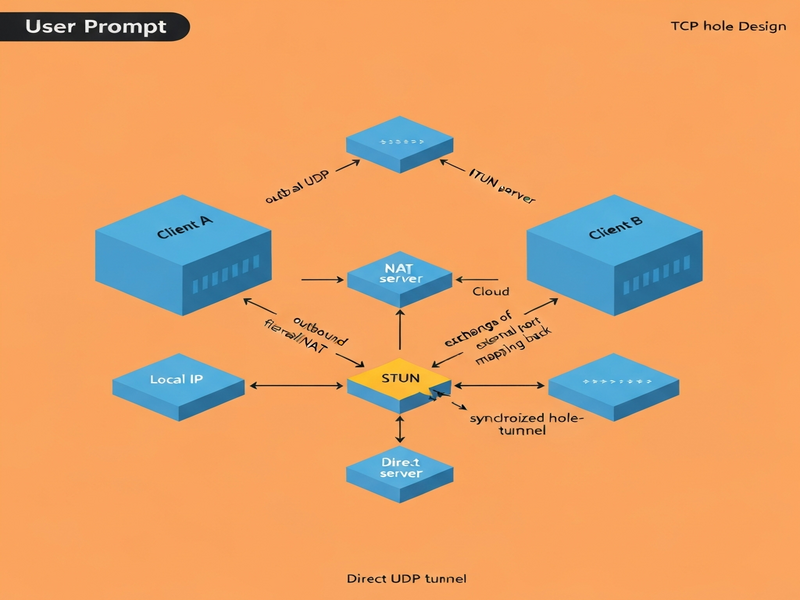
Figure 1: Step‑by‑step flow from bucket calculation to winner selection.
Further Reading
The original research article that introduced this deterministic method is available at Roberts’ TCP Hole Punching Documentation. It provides deeper mathematical proofs and additional performance benchmarks.
How UBOS Enhances Deterministic Networking
UBOS offers a suite of tools that complement deterministic TCP hole punching:
- Workflow automation studio – orchestrate the signaling phase with low‑code flows.
- UBOS pricing plans – choose a tier that includes high‑throughput networking modules.
- UBOS partner program – collaborate with telecom providers to embed deterministic NAT traversal in their edge devices.
- UBOS templates for quick start – launch a pre‑configured TCP hole‑punching service in minutes.
For startups looking to prototype quickly, the UBOS for startups page outlines a sandbox environment where you can test the algorithm against real‑world NAT devices without any upfront infrastructure cost.
Ready‑Made Templates That Leverage Deterministic Networking
The UBOS Template Marketplace hosts several AI‑enhanced apps that can be combined with deterministic TCP hole punching for richer experiences:
- Talk with Claude AI app – integrate a conversational AI that communicates directly over a peer‑to‑peer TCP channel.
- AI SEO Analyzer – run SEO audits on the client side without sending data to a cloud server.
- AI Video Generator – stream generated video frames over a deterministic TCP link for low‑latency playback.
- Generative AI Text-to-Video – collaborate on video creation between two remote editors using direct TCP sockets.
Conclusion
Deterministic TCP hole punching transforms the way peer‑to‑peer applications negotiate NAT traversal. By relying on a shared timestamp‑derived bucket, a reproducible port list, and a lightweight winner‑selection handshake, developers can eliminate costly relay infrastructure while preserving security and performance. Whether you are building a multiplayer game, a secure IoT mesh, or an AI‑driven collaboration tool, the algorithm offers a predictable, low‑overhead path to direct connectivity.
Ready to experiment? Visit the UBOS homepage to spin up a sandbox environment, explore the About UBOS story, and start building your own deterministic networking solution today.
