- Updated: February 18, 2026
- 5 min read
Google Trust Services Outage on 17 Feb 2026 Impacts Services – UBOS News
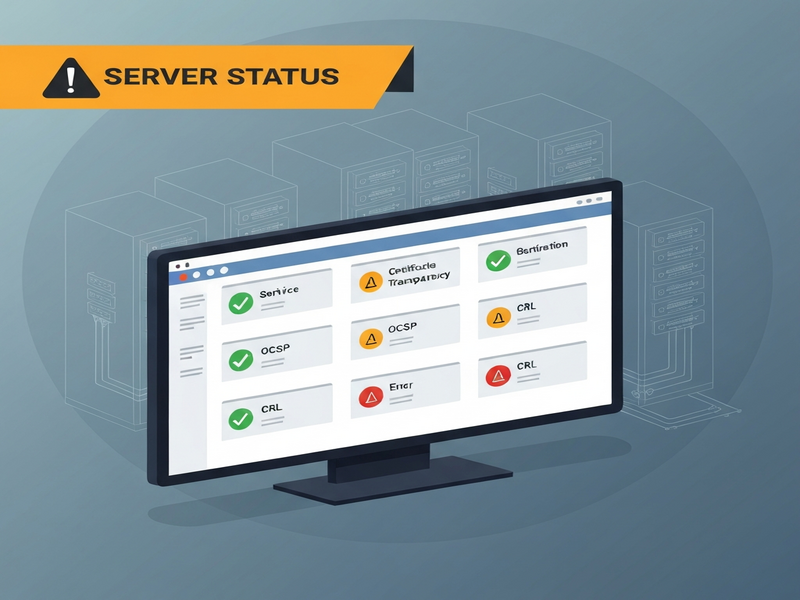
The Google Trust Services incident on 17 February 2026 temporarily halted SSL/TLS certificate issuance via the ACME API, but the issue was fully resolved by 21:04 PST the same day.
Incident Summary
On 17 February 2026, Google Trust Services (GTS) announced an unexpected service disruption that impacted its ACME API endpoints for both SXG and TLS certificate issuance. The outage forced a complete halt of new certificate generation for several hours, affecting developers, system administrators, and enterprises that rely on automated SSL/TLS provisioning. The incident was logged on the official Google PKI status page and later detailed in a formal incident report.
For security‑focused professionals, understanding the timeline, root causes, and mitigation steps is essential to prevent similar disruptions in their own PKI pipelines. This article provides a comprehensive, MECE‑structured analysis of the event, enriched with actionable insights and relevant UBOS homepage resources that can help you harden your certificate management workflows.
Detailed Timeline of Events
The GTS incident unfolded over a concise eight‑hour window. Below is a chronological breakdown, extracted from the official status feed:
| Time (PST) | Event |
|---|---|
| 11:32 | Initial rollout announced; issuance would be prevented. An estimate for the stop time was provided. |
| 12:14 | Issuance began to stop. Engineers projected an 8‑hour window for a fix. |
| 20:11 | Rollout required an additional two hours; the team apologized for the delay. |
| 21:05 | Fix deployed; issuance flow restored. Formal apology issued. |
All timestamps are in US/Pacific time. The incident lasted roughly 9 hours and 42 minutes from the first notice to full service restoration.
Impact Analysis
While the outage window was relatively short, its ripple effects were felt across multiple layers of the internet security ecosystem.
Affected Services
- ACME API for automated certificate issuance (both SXG and TLS).
- Third‑party CI/CD pipelines that depend on GTS for on‑the‑fly certificate provisioning.
- Managed hosting platforms that auto‑renew certificates via GTS.
Business Consequences
Enterprises that rely on continuous TLS renewal faced:
- Potential service downtime for web applications lacking valid certificates.
- Increased operational overhead as teams manually intervened to generate fallback certificates.
- Compliance concerns for regulated industries where certificate validity is audited.
For small‑to‑medium businesses (SMBs), the impact was amplified due to limited internal security staff. UBOS solutions for SMBs provide automated fallback mechanisms that can mitigate such interruptions.
Technical Repercussions
From a technical standpoint, the incident highlighted two key vulnerabilities in automated PKI pipelines:
- Single‑point dependency: Relying exclusively on a single CA’s API can create a bottleneck.
- Lack of graceful degradation: Most ACME clients did not have built‑in retry or fallback logic for prolonged outages.
Addressing these gaps is a core focus of modern UBOS platform overview, which offers multi‑CA orchestration and built‑in resilience patterns.
Response and Mitigation Steps
Google’s incident response team followed a structured approach:
1. Immediate Containment
Engineers halted the issuance pipeline to prevent the propagation of potentially malformed certificates. This decision, though disruptive, avoided a larger security risk.
2. Root Cause Investigation
Preliminary analysis pointed to a misconfiguration in the internal load‑balancer that routed ACME requests to a stale backend pool. The misrouting caused timeouts and forced the issuance service to enter a fail‑safe mode.
3. Patch Deployment
A configuration patch was rolled out at 20:11 PST, followed by a final fix at 21:05 PST. The rollout was staged across multiple regions to ensure stability.
4. Communication Strategy
Google maintained a live status page, posted regular updates, and sent email notifications to affected customers. Transparency helped reduce panic and allowed teams to plan manual workarounds.
5. Post‑Incident Recommendations
Google’s final report includes several best‑practice recommendations that align closely with capabilities offered by UBOS:
- Implement multi‑CA fallback using Chroma DB integration for certificate metadata storage.
- Leverage automated workflow orchestration via the Workflow automation studio to trigger alternative issuance paths.
- Adopt AI‑driven monitoring; for example, AI marketing agents can be repurposed to watch for certificate health anomalies.
- Utilize the Web app editor on UBOS to quickly prototype custom dashboards that surface real‑time PKI status.
Conclusion & Future Outlook
The February 2026 Google Trust Services incident serves as a reminder that even the most robust PKI providers can experience brief, high‑impact outages. For organizations that depend on continuous TLS, the key takeaways are:
- Redundancy is non‑negotiable: Deploy multi‑CA strategies and keep local fallback certificates ready.
- Automation with resilience: Use workflow engines—such as UBOS’s Workflow automation studio—to embed retry logic and alternative paths.
- Visibility and alerting: Integrate status feeds (e.g., Google’s PKI dashboard) into your monitoring stack.
- Continuous learning: Review post‑mortem reports and adapt your security policies accordingly.
Looking ahead, Google has pledged to enhance its ACME service reliability and to provide more granular status APIs. Meanwhile, the broader security community is expected to adopt more sophisticated PKI orchestration tools. UBOS’s Enterprise AI platform by UBOS already supports AI‑enhanced decision making for certificate lifecycle management, positioning it as a strategic partner for organizations seeking to future‑proof their TLS infrastructure.
Read the Full Incident Report
For a complete technical breakdown, see the original Google Trust Services incident report. The document includes timestamps, root‑cause analysis, and detailed remediation steps.
Related UBOS Resources
Enhance your security posture with these UBOS solutions:
- Telegram integration on UBOS – receive real‑time alerts directly in your messaging channels.
- ChatGPT and Telegram integration – automate incident triage with conversational AI.
- OpenAI ChatGPT integration – leverage large language models for security policy generation.
- ElevenLabs AI voice integration – turn alerts into audible notifications for on‑call engineers.
- UBOS templates for quick start – deploy pre‑built PKI monitoring dashboards in minutes.
- UBOS portfolio examples – see how other enterprises have built resilient certificate workflows.
- UBOS pricing plans – choose a plan that matches your security budget.
- About UBOS – learn more about our mission to democratize AI‑driven security.
- UBOS partner program – collaborate with us to integrate your own security tools.
- AI SEO Analyzer – ensure your security documentation is discoverable.
- AI Article Copywriter – generate compliance reports automatically.
© 2026 UBOS. All rights reserved.
