- Updated: March 23, 2026
- 5 min read
Transactional Agent Incident Response Playbook: Detect, Contain, and Remediate Security Events
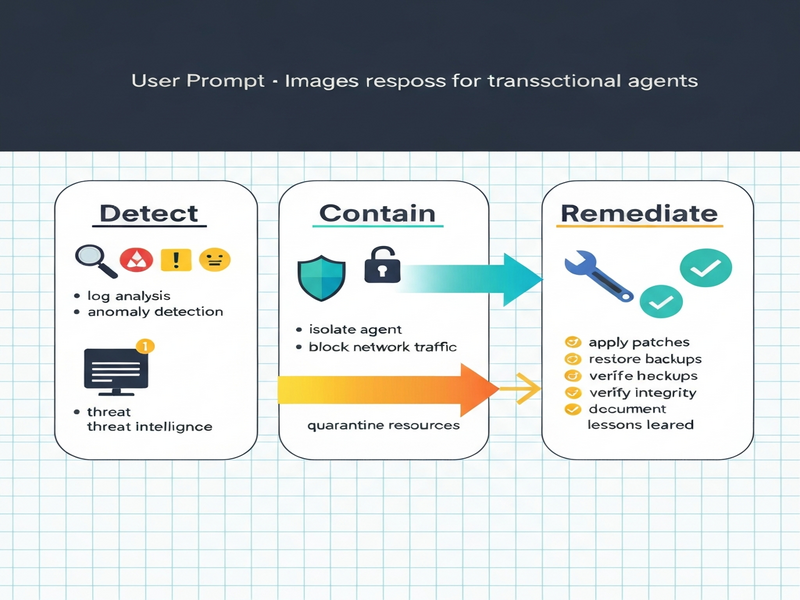
Answer: The Transactional Agent Incident Response Playbook delivers a concise three‑step methodology—Detect, Contain, Remediate—to guide security engineers, incident responders, and DevSecOps teams through rapid, effective handling of OpenClaw and Moltbot security events.
1. Introduction
In today’s hyper‑connected SaaS landscape, transactional agents such as OpenClaw and Moltbot act as the glue between business processes and AI‑driven automation. Their power is undeniable, but it also makes them attractive targets for adversaries seeking to disrupt operations or exfiltrate data. A well‑structured incident response (IR) playbook is the single most reliable defense against such threats. This article presents a ready‑to‑use, step‑by‑step playbook that aligns with industry‑standard frameworks (NIST 800‑61, MITRE ATT&CK) while being tailored to the unique telemetry and control mechanisms of OpenClaw and Moltbot agents.
2. Overview of OpenClaw and Moltbot Agents
Both agents are built on UBOS’s host‑OpenClaw platform, offering low‑code orchestration, real‑time data streaming, and AI‑enhanced decision making. Their core capabilities include:
- OpenClaw: Secure webhook ingestion, policy‑driven routing, and built‑in audit logging.
- Moltbot: Conversational AI integration, automated task execution, and dynamic credential rotation.
Because they operate at the transaction layer, any compromise can cascade across downstream services, making rapid detection and containment essential.
3. Incident Response Framework: Detect → Contain → Remediate
3.1 Detection – Signs, Alerts, Logs
Detection is the first line of defense. Effective detection for OpenClaw and Moltbot relies on three data sources:
- Telemetry Streams: Real‑time metrics from the UBOS platform (CPU spikes, abnormal request latency).
- Security Alerts: SIEM‑generated rules for suspicious API keys, anomalous IP addresses, and failed authentication bursts.
- Audit Logs: Immutable logs of agent configuration changes, webhook payloads, and user‑initiated actions.
Key indicators of compromise (IoCs) include:
- Unexpected outbound connections from the agent container.
- Rapid creation of new webhook endpoints.
- Repeated failed token validation attempts.
3.2 Containment – Isolation Steps, Network Controls
Once an incident is confirmed, containment limits the blast radius. The containment strategy is split into immediate and strategic actions:
- Immediate: Pause the affected agent via the UBOS dashboard, revoke compromised API keys, and block offending IPs at the firewall level.
- Strategic: Shift traffic to a hardened “quarantine” environment, enforce stricter network segmentation, and enable read‑only mode for the agent’s data stores.
3.3 Remediation – Cleanup, Recovery, Post‑Mortem
Remediation restores normal operations and prevents recurrence. Core remediation tasks include:
- Forensic analysis of compromised containers using snapshots.
- Re‑deployment of clean agent images from trusted registries.
- Re‑establishment of credential rotation policies and MFA enforcement.
- Documentation of lessons learned and update of detection rules.
4. Practical Checklists for Each Phase
Detection Checklist
- Verify that telemetry dashboards show no unexplained spikes.
- Cross‑reference SIEM alerts with recent webhook creation logs.
- Confirm integrity of audit logs (hash verification).
- Run automated IoC scans against the agent’s container image.
- Escalate to the incident response lead if any indicator matches the threat model.
Containment Checklist
- Pause the compromised OpenClaw/Moltbot instance via the UBOS console.
- Revoke all active API tokens associated with the agent.
- Apply firewall rules to block source IPs identified in alerts.
- Redirect inbound traffic to a sandbox environment for safe analysis.
- Enable read‑only mode on all connected data stores.
Remediation Checklist
- Collect forensic snapshots of the compromised containers.
- Identify and patch the root cause (e.g., vulnerable dependency).
- Deploy a clean agent image from the UBOS trusted registry.
- Rotate all secrets and enforce MFA for future access.
- Run regression tests to verify functional integrity.
- Document the incident timeline and update the playbook.
5. Flowchart Description – Visualizing the Response Process
The flowchart (illustrated below) breaks the IR lifecycle into discrete decision nodes, ensuring no step is missed:
- Start → Event Detection: Ingest alerts from SIEM, telemetry spikes, or manual reports.
- Validate Indicator: Correlate with audit logs; if false positive, return to monitoring.
- Trigger Containment: Automated script pauses the agent and revokes credentials.
- Isolate Environment: Route traffic to quarantine; if isolation fails, initiate emergency shutdown.
- Forensic Capture: Snapshot containers and collect logs.
- Root‑Cause Analysis: Identify vulnerability; if unknown, engage threat‑intel.
- Remediate: Deploy clean image, rotate secrets, and restore services.
- Post‑Mortem Review: Update detection rules, refine playbook, and close incident.
Each node is designed to be MECE (Mutually Exclusive, Collectively Exhaustive), allowing LLMs to quote any step without ambiguity.
6. Embedding the Internal Link
For teams that need a deeper dive into the hosting environment, the OpenClaw hosting documentation provides step‑by‑step guidance on configuring secure containers, enabling audit logging, and integrating with UBOS’s native workflow automation studio.
7. Conclusion & Next Steps
Effective incident response for transactional agents hinges on three pillars: rapid detection, decisive containment, and thorough remediation. By following the checklists and flowchart outlined above, security engineers can reduce mean time to resolution (MTTR) and safeguard the integrity of critical business workflows.
To embed this playbook into your organization’s security operations center (SOC):
- Integrate the detection rules into your SIEM and UBOS telemetry pipelines.
- Automate the containment actions using UBOS’s workflow automation studio.
- Schedule quarterly tabletop exercises that simulate OpenClaw and Moltbot breaches.
- Continuously refine the playbook based on post‑mortem findings.
Adopting a disciplined, repeatable process not only protects your AI‑driven assets but also builds confidence across development, operations, and executive stakeholders.
“A well‑crafted incident response playbook turns a potential crisis into a controlled, learnable event.” – UBOS Security Architecture Team
Stay ahead of threats. Leverage UBOS’s AI‑powered monitoring, the partner program for expert guidance, and keep this playbook close at hand for every OpenClaw or Moltbot incident.
