UBOS Asset Marketplace: MCP Server for Proactive Threat Intelligence
In today’s dynamic threat landscape, staying ahead of cyber threats requires more than just reactive measures. Organizations need proactive threat intelligence to identify vulnerabilities, anticipate attacks, and mitigate risks effectively. The UBOS Asset Marketplace offers a powerful solution: the MCP (Model Context Protocol) Server specifically designed for threat information collection.
What is an MCP Server and Why is it Crucial for Cybersecurity?
An MCP server, at its core, acts as a critical bridge between AI models and external data sources. Following the open MCP protocol, it standardizes how applications provide contextual information to Large Language Models (LLMs) and other AI systems. In the context of cybersecurity, this means enabling AI-powered security tools to access, process, and understand threat intelligence data from various sources.
Think of it as a universal translator for security information. Instead of relying on disparate data formats and integration methods, the MCP server provides a consistent and reliable way for AI to consume threat data, leading to faster and more accurate threat detection and response.
Use Cases: Unleashing the Power of Automated Threat Intelligence
The MCP Server for threat info collection empowers a wide range of cybersecurity use cases, including:
- Automated Threat Data Aggregation: Automatically collect and aggregate threat intelligence data from diverse sources, such as threat feeds, vulnerability databases, and security blogs. This eliminates the need for manual data collection, saving valuable time and resources.
- Enhanced Threat Detection: Feed aggregated threat data to AI-powered threat detection systems to improve their accuracy and reduce false positives. By providing rich contextual information, the MCP server enables AI models to identify subtle patterns and anomalies that might otherwise go unnoticed.
- Proactive Vulnerability Management: Identify and prioritize vulnerabilities based on real-time threat intelligence. By understanding which vulnerabilities are actively being exploited in the wild, organizations can focus their remediation efforts on the most critical risks.
- Incident Response Automation: Automate incident response workflows by providing AI models with the context they need to make informed decisions. For example, an MCP server can provide information about the affected systems, the type of attack, and the potential impact, enabling AI to automatically contain and remediate the incident.
- Threat Hunting: Empower threat hunters with AI-driven tools that can analyze vast amounts of data and identify hidden threats. The MCP server provides access to the data these tools need to uncover malicious activity and prevent future attacks.
- Neo4j Knowledge Graph Integration: The provided configuration allows seamless integration with Neo4j, a graph database, enabling you to build a knowledge graph of threats and their relationships. This unlocks powerful analytics and visualization capabilities, allowing you to gain deeper insights into the threat landscape.
Key Features: Streamlining Threat Intelligence Workflows
The MCP Server for threat info collection offers a range of features designed to streamline threat intelligence workflows and improve security posture:
- Configurable Data Sources: Easily configure the MCP server to collect data from a variety of sources, including threat feeds, vulnerability databases, and security blogs. This allows you to tailor the data collection process to your specific needs.
- Data Transformation and Enrichment: Transform and enrich raw threat data to improve its quality and usability. This includes normalizing data formats, removing duplicates, and adding contextual information.
- Real-Time Data Updates: Receive real-time updates on new threats and vulnerabilities. This ensures that your threat intelligence data is always up-to-date and accurate.
- API Integration: Integrate the MCP server with your existing security tools and workflows via a simple and intuitive API. This allows you to seamlessly incorporate threat intelligence data into your security operations.
- Flexible Deployment Options: Deploy the MCP server on-premises or in the cloud, depending on your specific requirements. This provides maximum flexibility and scalability.
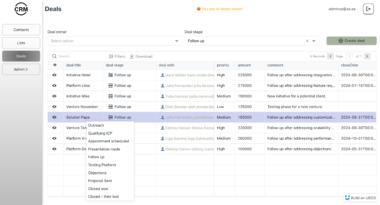
- Smithery Integration: Visualize and manage your MCP server configurations within the Smithery interface (as demonstrated in the provided image), providing a user-friendly way to control your threat intelligence collection.
Leveraging UBOS for AI Agent Orchestration and Customization
The UBOS platform takes the power of the MCP Server for threat info collection even further. As a full-stack AI Agent Development Platform, UBOS enables you to:
- Orchestrate AI Agents: Seamlessly integrate the MCP server with other AI agents to automate complex security tasks.
- Connect to Enterprise Data: Connect the MCP server to your enterprise data sources to enrich threat intelligence data with internal context.
- Build Custom AI Agents: Build custom AI agents that leverage the MCP server to address specific security challenges.
- Multi-Agent Systems: Develop multi-agent systems that can collaborate to provide comprehensive threat protection.
Example Configuration and Usage
The provided mcp.json configuration demonstrates how to set up the MCP server to collect threat news using the collect_threat_info tool. This tool is configured to collect threat information for a specific date range (March 1-10, 2024) and stores it in the /Users/sheldon/Desktop/mcp_test/threatmcp directory.
mcp.json Configuration Breakdown:
Threat_newsServer: This configuration defines an MCP server namedThreat_newsthat executes thecollect.pyscript using theuvcommand within the specified directory.command: Specifies the command to execute (in this case,uv).args: Provides arguments to the command, including the directory and the script to run.env: Sets environment variables, such as theAPI_KEYrequired for accessing threat intelligence data.
neo4jServer: This configuration sets up an MCP server to interact with a Neo4j graph database.command: Specifies the command to execute (in this case,npx).args: Provides arguments to the command, including the@alanse/mcp-neo4j-serverpackage.env: Sets environment variables required for connecting to the Neo4j database, including the URI, username, and password.
Tool Usage Example:
{ “TOOL”: “collect_threat_info”, “arguments”: { “start_year”: “2024”, “start_month”: “3”, “start_day”: “1”, “end_year”: “2024”, “end_month”: “3”, “end_day”: “10” } }
This JSON snippet demonstrates how to invoke the collect_threat_info tool with specific start and end dates to collect threat data for that period.
Benefits of Using the UBOS Asset Marketplace MCP Server
- Proactive Threat Protection: Stay ahead of emerging threats with real-time threat intelligence.
- Improved Threat Detection: Enhance the accuracy of your threat detection systems by providing them with rich contextual information.
- Automated Incident Response: Automate incident response workflows to reduce the time it takes to contain and remediate attacks.
- Reduced Security Costs: Automate manual security tasks and improve the efficiency of your security operations.
- Enhanced Security Posture: Strengthen your overall security posture by leveraging the power of AI and threat intelligence.
Conclusion: Empowering Your Cybersecurity with UBOS
The UBOS Asset Marketplace MCP Server for threat info collection is a powerful tool for organizations looking to improve their cybersecurity posture. By automating threat intelligence workflows and providing AI models with the context they need to make informed decisions, this solution helps organizations stay ahead of emerging threats and protect their critical assets. Embrace the future of cybersecurity with UBOS and unlock the power of AI-driven threat intelligence.
Threat News
Project Details
- xue20010808/ThreatNews
- MIT License
- Last Updated: 4/14/2025
Recomended MCP Servers
Model Context Protocol (MCP) server for @glideapps API
MCP server for Gmail integration
TEST
MCP-NixOS - Model Context Protocol Server for NixOS resources
这是一个针对于MySQL开发的MCP,该项目旨在帮助用户快速且精确的查询MySQL数据库中的内容
A Model Context Protocol server for interacting with the Solana blockchain, powered by the Solana Agent Kit (https://github.com/sendaifun/solana-agent-kit)
程序员延寿指南 | A programmer's guide to live longer
This read-only MCP Server allows you to connect to HubSpot data from Claude Desktop through CData JDBC Drivers....
Config files for my GitHub profile.
📢 Instagram MCP Server – A powerful Model Context Protocol (MCP) server for tracking Instagram engagement, generating leads,...