NmapMCP: Unleash the Power of Network Scanning in Your AI Agent Ecosystem
In the ever-evolving landscape of cybersecurity and network management, the ability to efficiently and effectively scan networks for vulnerabilities and potential threats is paramount. Nmap, a widely respected and powerful network scanning tool, has long been a staple in the arsenals of security professionals and network administrators. Now, with NmapMCP, this capability is seamlessly integrated into Model Context Protocol (MCP) environments, opening up a new realm of possibilities for AI-powered security and automation.
NmapMCP is a robust integration of the Nmap scanning tool with the Model Context Protocol (MCP). This integration empowers AI agents to leverage Nmap’s extensive scanning capabilities directly within MCP-compatible environments. By bridging the gap between network scanning and AI-driven automation, NmapMCP unlocks a new level of efficiency, accuracy, and proactivity in network security and management.
Key Features That Set NmapMCP Apart
NmapMCP boasts a comprehensive suite of features designed to address a wide range of network scanning needs. From identifying open ports and detecting operating systems to conducting stealthy scans and mapping network topologies, NmapMCP provides the tools necessary to gain deep insights into your network’s security posture.
- Top Ports Scanning: Quickly identify the most commonly used ports on target hosts to assess potential entry points. This feature allows security professionals to prioritize their efforts by focusing on the most likely attack vectors.
- DNS Brute Force: Discover subdomains associated with a target domain, aiding in comprehensive domain mapping. This is crucial for identifying all potential entry points and understanding the full scope of an organization’s online presence.
- List Scan: Obtain a list of active hosts within a specified range without port scanning, useful for network inventory. This feature provides a quick and efficient way to identify all active devices on a network, enabling administrators to maintain an accurate inventory of their assets.
- OS Detection: Determine the operating system of a target host by analyzing network responses, assisting in vulnerability assessment. Knowing the operating system allows security professionals to identify known vulnerabilities and tailor their security measures accordingly.
- Version Detection: Identify service versions running on open ports to detect outdated or vulnerable services. Outdated software is a common target for attackers, making version detection a critical component of a comprehensive security strategy.
- FIN Scan: Perform stealthy scans by sending FIN packets to detect open ports without establishing a full connection. This technique can help evade detection by firewalls and intrusion detection systems.
- Idle Scan: Conduct highly stealthy scans by leveraging idle hosts to probe target systems, minimizing detection risks. Idle scanning is a more sophisticated technique that makes it even harder for attackers to be detected.
- Ping Scan: Detect active hosts in a network by sending ICMP echo requests, useful for network mapping. This is a basic but essential technique for identifying live hosts on a network.
- SYN Scan: Perform half-open TCP scans to identify open ports without completing the TCP handshake, reducing detection likelihood. SYN scanning is a faster and less intrusive method of port scanning than TCP Connect scanning.
- TCP Connect Scan: Establish full TCP connections to probe open ports, useful when SYN scans are not feasible. This method is more reliable than SYN scanning but also more easily detected.
- UDP Scan: Identify open UDP ports on a target host to detect services that do not use TCP. UDP scanning is essential for identifying services that communicate over UDP, such as DNS and DHCP.
- Port Scan Only: Focus solely on scanning ports without additional host discovery, streamlining the scanning process. This feature allows security professionals to quickly identify open ports without wasting time on host discovery.
- No Port Scan: Perform host discovery without scanning ports, useful for identifying live hosts without probing services. This feature is useful for quickly identifying active hosts without revealing your intentions.
- ARP Discovery: Identify active devices within a local network segment using ARP requests, effective in LAN environments. ARP discovery is a fast and reliable method of identifying devices on a local network.
- Disable DNS Resolution: Perform scans without resolving IP addresses to hostnames, enhancing scan speed and reducing DNS query traffic. This feature can significantly speed up scanning, especially when scanning large networks.
Use Cases: Where NmapMCP Shines
The versatility of NmapMCP makes it a valuable asset in a wide range of use cases, including:
- Vulnerability Assessment: Proactively identify vulnerabilities in your network infrastructure by scanning for open ports, outdated software versions, and misconfigurations. NmapMCP can be integrated into automated vulnerability assessment workflows to continuously monitor your network for potential weaknesses.
- Penetration Testing: Simulate real-world attacks to assess the effectiveness of your security controls. NmapMCP provides penetration testers with the tools they need to identify and exploit vulnerabilities in a controlled environment.
- Network Inventory: Maintain an accurate inventory of all devices and services on your network. NmapMCP can be used to automatically discover and identify all active devices, making it easier to manage and secure your network.
- Security Monitoring: Continuously monitor your network for suspicious activity and potential threats. NmapMCP can be integrated into security information and event management (SIEM) systems to provide real-time alerts and insights into network security events.
- Compliance Auditing: Ensure compliance with industry regulations and security standards. NmapMCP can be used to generate reports that demonstrate your organization’s adherence to security best practices.
Installation and Configuration: Getting Started with NmapMCP
NmapMCP can be installed either manually or through Smithery, a platform for managing and deploying AI agents. The installation process is straightforward, and the configuration file allows you to customize the tool’s behavior to suit your specific needs.
Installation via Smithery:
The easiest way to install NmapMCP is through Smithery. Simply run the following command in your terminal:
bash npx -y @smithery/cli install @0xPratikPatil/nmapmcp --client claude
Manual Installation:
To install NmapMCP manually, follow these steps:
Clone the repository:
bash git clone https://github.com/0xPratikPatil/NmapMCP.git cd NmapMCP
Install
uv:bash curl -LsSf https://astral.sh/uv/install.sh | sh
Create environment: bash uv venv
Install dependencies from
pyproject.toml:bash uv pip install
or bash uv pip install -r pyproject.toml
Configuration:
To configure NmapMCP, edit the claude_desktop_config.json file located in the project root. This file allows you to set default scan arguments, define MCP tool behaviors, and adjust logging settings.
Contributing to NmapMCP: Join the Community
NmapMCP is an open-source project, and contributions are welcome from developers and security enthusiasts of all levels. If you’re interested in contributing, you can fork the repository, create a new branch, make your changes, and submit a pull request.
License and Acknowledgments
NmapMCP is licensed under the MIT License. The project also acknowledges the invaluable contributions of the Nmap and MCP communities.
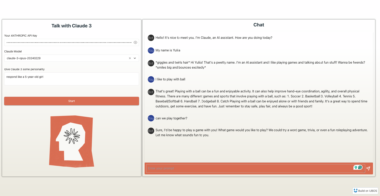
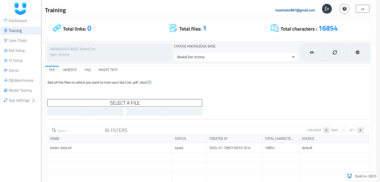
Unlock the Full Potential of AI-Powered Security with UBOS
NmapMCP represents a significant step forward in the integration of AI and cybersecurity. By combining the power of Nmap with the flexibility of MCP, NmapMCP empowers AI agents to proactively identify and address network security threats. This integration makes NmapMCP a valuable addition to the UBOS platform.
UBOS (ubos.tech) is a full-stack AI Agent Development Platform designed to bring AI Agent capabilities to every business department. UBOS provides a comprehensive suite of tools and services for orchestrating AI Agents, connecting them with enterprise data, building custom AI Agents with your LLM model, and creating Multi-Agent Systems. By integrating NmapMCP into the UBOS ecosystem, organizations can unlock the full potential of AI-powered security automation and create a more secure and resilient network environment. UBOS enables businesses to seamlessly manage and deploy AI Agents, ensuring they are well-integrated with existing infrastructure and workflows. This strategic approach enhances overall operational efficiency and security posture.
UBOS users can leverage NmapMCP within their AI Agent workflows to automate vulnerability assessments, penetration testing, and security monitoring. For example, an AI Agent could be configured to automatically scan the network for new vulnerabilities, generate reports, and even take automated remediation steps. UBOS’s intuitive interface and robust features make it easy to integrate NmapMCP and other security tools into your AI Agent ecosystem.
In conclusion, NmapMCP is a powerful tool that enhances network scanning capabilities within MCP environments, making it an invaluable asset for organizations seeking to leverage AI in their security operations. When combined with the comprehensive features of the UBOS platform, NmapMCP becomes an integral part of a robust, AI-driven security strategy, enabling businesses to protect their networks more effectively and efficiently.
Nmap Integration
Project Details
- 0xPratikPatil/NmapMCP
- Last Updated: 5/11/2025
Recomended MCP Servers
查询天气的mcp服务器
browser-use mcp server
Official Firecrawl MCP Server - Adds powerful web scraping to Cursor, Claude and any other LLM clients.
A Model Context Protocol server for Chess.com's Published Data API. This provides access to Chess.com player data, game...
Break free of your MCP Client constraints 🦹
MCP web search using perplexity without any API KEYS
Multiple use cases unlocked by Browser use agent
A Model Context Protocol Server for Interacting with Slack