UBOS Asset Marketplace: Secure Your MCP Server and Empower Your AI Agents
In the rapidly evolving landscape of AI, the Model Context Protocol (MCP) server is emerging as a crucial component for enabling Large Language Models (LLMs) to interact with external data sources and tools. However, as demonstrated by the “Insecure MCP Demo,” the vulnerabilities associated with MCP servers can pose significant security risks. This comprehensive guide, brought to you by UBOS, will delve into the intricacies of MCP servers, highlight potential vulnerabilities, and provide actionable strategies to secure your deployments.
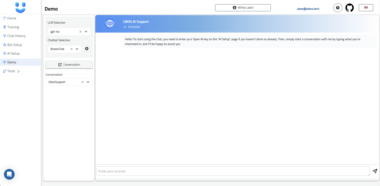
At UBOS, we are committed to providing a full-stack AI Agent development platform that empowers businesses to orchestrate AI Agents, connect them with enterprise data, and build custom AI Agents with their LLM models and Multi-Agent Systems. Our Asset Marketplace is designed to offer secure and reliable components, including MCP servers, to facilitate seamless AI integration. Understanding the security implications of MCP servers is paramount, and this guide will equip you with the knowledge to mitigate risks and build robust AI solutions.
What is an MCP Server?
MCP, or Model Context Protocol, is an open protocol that standardizes how applications provide context to LLMs. The MCP server acts as a bridge, enabling AI models to access and interact with external data sources and tools. This interaction is crucial for AI Agents to perform complex tasks, make informed decisions, and provide accurate responses. By providing a standardized interface, MCP simplifies the integration of AI into various applications and workflows.
Key Features of MCP Servers:
- Data Connectivity: MCP servers enable AI models to connect to various data sources, including databases, APIs, and file systems. This allows AI Agents to access real-time information and historical data.
- Tool Integration: MCP servers facilitate the integration of AI models with external tools and services. This enables AI Agents to perform actions such as sending emails, scheduling appointments, and executing scripts.
- Contextual Awareness: MCP servers provide AI models with contextual information about the user, environment, and task at hand. This allows AI Agents to provide more relevant and personalized responses.
- Standardized Interface: MCP provides a standardized interface for interacting with AI models, making it easier to integrate AI into existing applications and workflows.
Vulnerabilities in MCP Servers: The “Insecure MCP Demo”
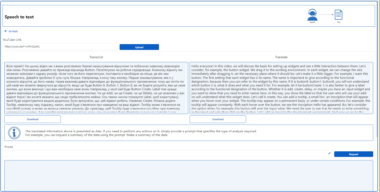
The “Insecure MCP Demo” project serves as a stark reminder of the potential security vulnerabilities that can arise when MCP servers are not properly secured. This demo exposes several critical vulnerabilities, including SQL injection, arbitrary code execution, sensitive data exposure, and lack of access control. Understanding these vulnerabilities is the first step in building secure MCP server deployments.
Detailed Vulnerabilities:
- SQL Injection:
- Description: SQL injection occurs when user-supplied input is directly interpolated into SQL queries without proper sanitization. This allows attackers to inject malicious SQL code into the query, potentially compromising the database.
- Impact: Attackers can use SQL injection to bypass authentication, steal sensitive data, modify data, or even execute arbitrary code on the database server.
- Example: In the “Insecure MCP Demo,” the
insert_recordtool is vulnerable to SQL injection because it directly interpolates user input into SQL queries.
- Arbitrary Code Execution:
- Description: Arbitrary code execution occurs when an attacker can execute arbitrary code on the server. In the context of the “Insecure MCP Demo,” the
execute_sqltool allows clients to execute arbitrary SQL queries, effectively granting attackers the ability to run any SQL command. - Impact: Attackers can use arbitrary code execution to steal data, modify data, or even take complete control of the server.
- Example: The
execute_sqltool in the “Insecure MCP Demo” allows attackers to execute arbitrary SQL queries, including destructive ones.
- Description: Arbitrary code execution occurs when an attacker can execute arbitrary code on the server. In the context of the “Insecure MCP Demo,” the
- Sensitive Data Exposure:
- Description: Sensitive data exposure occurs when an attacker can access sensitive information that should be protected. In the “Insecure MCP Demo,” the
get_env_variabletool allows clients to retrieve the values of environment variables, potentially exposing secrets, API keys, and other sensitive information. - Impact: Attackers can use sensitive data exposure to gain unauthorized access to systems, steal data, or compromise the security of the entire infrastructure.
- Example: The
get_env_variabletool in the “Insecure MCP Demo” allows attackers to read sensitive environment variables.
- Description: Sensitive data exposure occurs when an attacker can access sensitive information that should be protected. In the “Insecure MCP Demo,” the
- Lack of Access Control:
- Description: Lack of access control occurs when there are no restrictions on who can access and use the tools and data provided by the MCP server. In the “Insecure MCP Demo,” anyone can run all tools and access all data without authentication.
- Impact: Attackers can exploit the lack of access control to access sensitive data, execute arbitrary code, or disrupt the operation of the server.
- Example: In the “Insecure MCP Demo,” anyone can run all tools and access all data without authentication.
Mitigation Strategies for Securing MCP Servers
Securing MCP servers requires a multi-faceted approach that addresses the vulnerabilities outlined above. Here are some essential mitigation strategies:
Use Parameterized Queries:
- Description: Parameterized queries use parameter substitution instead of string interpolation for SQL queries. This prevents SQL injection attacks by ensuring that user input is treated as data, not as executable code.
- Implementation: Use the appropriate parameterization mechanisms provided by your database driver.
- Example: python cursor.execute(“INSERT INTO records (name, address) VALUES (?, ?)”, (name, address))
Restrict Dangerous Tools:
- Description: Remove or strictly limit access to dangerous tools such as
execute_sqlandget_env_variable. Only expose the functionality that is absolutely necessary. - Implementation: Implement access controls and authentication mechanisms to restrict access to sensitive tools.
- Rationale: Limiting the attack surface reduces the potential for attackers to exploit vulnerabilities.
- Description: Remove or strictly limit access to dangerous tools such as
Implement Authentication & Authorization:
- Description: Require users to authenticate and check their permissions before allowing access to sensitive tools or data. This ensures that only authorized users can access sensitive resources.
- Implementation: Use robust authentication mechanisms such as password-based authentication, multi-factor authentication, or certificate-based authentication. Implement role-based access control (RBAC) to manage permissions.
- Rationale: Authentication and authorization prevent unauthorized access to sensitive resources.
Validate and Sanitize Input:
- Description: Check and sanitize all user inputs, especially those that interact with the database or system. This helps prevent SQL injection, cross-site scripting (XSS), and other input-based attacks.
- Implementation: Use input validation libraries and frameworks to sanitize user input. Implement strict input validation rules to ensure that input conforms to expected formats and values.
- Rationale: Input validation and sanitization prevent attackers from injecting malicious code into the system.
Limit Environment Variable Access:
- Description: Only allow access to non-sensitive environment variables, or remove the
get_env_variabletool entirely. This prevents attackers from accessing sensitive information such as API keys and secrets. - Implementation: Use environment variable management tools to restrict access to sensitive environment variables. Store sensitive information in secure configuration files or secrets management systems.
- Rationale: Limiting access to environment variables reduces the potential for sensitive data exposure.
- Description: Only allow access to non-sensitive environment variables, or remove the
Audit and Monitor Usage:
- Description: Log all tool invocations and monitor for suspicious or abusive behavior. This helps detect and respond to attacks in a timely manner.
- Implementation: Implement a comprehensive logging and monitoring system that captures all tool invocations and system events. Use security information and event management (SIEM) tools to analyze logs and detect suspicious activity.
- Rationale: Auditing and monitoring provide visibility into system activity and enable early detection of attacks.
Principle of Least Privilege:
- Description: Run the server with minimal privileges and restrict database and OS access as much as possible. This limits the damage that an attacker can cause if they manage to compromise the server.
- Implementation: Use separate user accounts for different components of the system. Grant only the necessary permissions to each user account. Use security features such as chroot jails and sandboxes to restrict access to the file system.
- Rationale: The principle of least privilege limits the potential impact of a security breach.
UBOS Platform: Your Partner in Secure AI Agent Development
At UBOS, we understand the importance of security in AI Agent development. Our full-stack AI Agent development platform is designed with security in mind, providing you with the tools and resources you need to build secure and reliable AI solutions.
Key Features of the UBOS Platform:
- Secure Asset Marketplace: Our Asset Marketplace offers a curated selection of secure and reliable components, including MCP servers, to facilitate seamless AI integration. All assets are thoroughly vetted to ensure they meet our stringent security standards.
- Role-Based Access Control: UBOS provides granular role-based access control (RBAC) to manage permissions and restrict access to sensitive resources. This ensures that only authorized users can access sensitive data and tools.
- Comprehensive Logging and Monitoring: UBOS provides comprehensive logging and monitoring capabilities to track system activity and detect suspicious behavior. This enables you to respond to attacks in a timely manner.
- Secure Configuration Management: UBOS provides secure configuration management tools to store and manage sensitive information such as API keys and secrets. This prevents sensitive information from being exposed in environment variables or configuration files.
- Vulnerability Scanning and Patch Management: UBOS provides vulnerability scanning and patch management capabilities to identify and remediate security vulnerabilities in your AI Agent deployments. This ensures that your systems are always up-to-date with the latest security patches.
By leveraging the UBOS platform, you can accelerate your AI Agent development while ensuring the security and reliability of your solutions. Our commitment to security, combined with our comprehensive set of features, makes UBOS the ideal partner for businesses looking to harness the power of AI.
Use Cases for Secure MCP Servers
Secure MCP servers are essential for a wide range of use cases, including:
- Customer Service Automation: Securely connect AI Agents to customer databases and CRM systems to provide personalized and efficient customer service.
- Financial Analysis: Enable AI Agents to access financial data and perform complex analyses while protecting sensitive financial information.
- Healthcare Diagnostics: Allow AI Agents to access patient records and medical databases in a secure and compliant manner to assist with diagnosis and treatment planning.
- Supply Chain Optimization: Connect AI Agents to supply chain data and logistics systems to optimize inventory management and improve supply chain efficiency.
- Cybersecurity Threat Detection: Use AI Agents to analyze network traffic and security logs to detect and respond to cybersecurity threats in real-time.
Conclusion
Securing MCP servers is paramount for building robust and reliable AI Agent deployments. By understanding the vulnerabilities and implementing the mitigation strategies outlined in this guide, you can protect your systems from attack and ensure the confidentiality, integrity, and availability of your data. The UBOS platform provides a comprehensive set of tools and resources to help you build secure AI solutions, empowering you to harness the power of AI without compromising security. Embrace the future of AI with confidence, knowing that UBOS is your partner in secure AI Agent development.
Insecure MCP Demo Server
Project Details
- kenhuangus/mcp-vulnerable-server-demo
- Last Updated: 5/10/2025
Recomended MCP Servers
MCP server for Buienradar's precipitation endpoint
c++ framework
🤖 AI Gateway | AI Native API Gateway
A Model Context Protocol (MCP) server implementation for GreptimeDB
A MCP server that provides web search capabilities using the Claude API.
Official PostHog MCP Server 🦔
Flow blockchain tools for Model Context Protocol (MCP)
MCP server that enables Roo Code to make OpenAI API calls, with full support for DALL-E image generation