MCP Server for Ghidra: Revolutionizing Reverse Engineering
In the ever-evolving landscape of cybersecurity and software analysis, the ability to decompile and analyze binary files efficiently is a game-changer. Enter the MCP Server for Ghidra—a powerful tool that transforms Ghidra into an interactive reverse-engineering backend. By leveraging the Model Context Protocol (MCP), this server bridges the gap between decompiled binary data and Large Language Models (LLMs), enabling seamless data extraction and analysis.
Key Features
1. Decompilation in Headless Mode
The MCP Server utilizes Ghidra’s headless mode to decompile binaries, extracting rich data such as function pseudocode, names, parameters, variables, strings, comments, and more. This feature allows users to automate the decompilation process, saving time and effort.
2. Comprehensive Data Extraction
With the ability to extract data structures, enums, and function definitions, the MCP Server provides a holistic view of the binary’s architecture. This comprehensive data extraction is crucial for in-depth analysis and understanding of complex software systems.
3. JSON Output for Easy Integration
The extracted data is outputted to a ghidra_context.json file, making it easily integrable with other tools and platforms. This JSON format ensures that the data is accessible and usable for further analysis or integration with other systems.
4. Exposing Tools via MCP
The server exposes a suite of tools through the MCP, including functions like list_functions(), get_pseudocode(name), list_structures(), and more. These tools provide users with the flexibility to query and interact with the decompiled data programmatically.
5. Cross-Platform Compatibility
Tested on macOS, the MCP Server requires Python 3.10+, Ghidra 11.3.1+, Java 21, and an MCP client like Claude Desktop. This cross-platform compatibility ensures that users can deploy the server in diverse environments.
Use Cases
1. Cybersecurity Analysis
For cybersecurity professionals, the MCP Server is an invaluable tool for analyzing malware binaries. By extracting detailed function and structure data, analysts can gain insights into the malware’s behavior and potential vulnerabilities.
2. Software Reverse Engineering
Software engineers and developers can use the MCP Server to reverse engineer proprietary software, understanding its architecture and functionality. This capability is essential for compatibility assessments and feature replication.
3. Academic Research
In academia, the MCP Server facilitates research in binary analysis and reverse engineering. Researchers can use the server to study binary structures and develop new analysis techniques.
4. AI and Machine Learning
By integrating with LLMs, the MCP Server opens new avenues for AI-driven binary analysis. Machine learning models can be trained to identify patterns and anomalies in decompiled data, enhancing automated analysis capabilities.
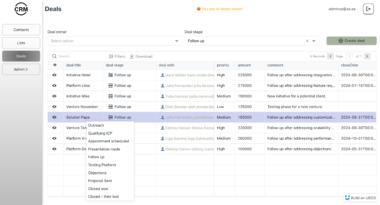
UBOS Platform Integration
UBOS, a full-stack AI Agent Development Platform, complements the MCP Server by providing a robust environment for orchestrating AI Agents. By connecting AI Agents with enterprise data, UBOS enables businesses to build custom AI solutions tailored to their specific needs. The integration of MCP Server with UBOS enhances the platform’s capabilities, allowing for advanced data analysis and AI-driven insights.
Conclusion
The MCP Server for Ghidra is a revolutionary tool that empowers users to transform binary data into actionable insights. By leveraging the power of Ghidra and MCP, the server provides a seamless integration with LLMs, enabling advanced analysis and data extraction. Whether you’re in cybersecurity, software engineering, or academia, the MCP Server is an essential tool for your reverse engineering toolkit.
Ghidra Reverse Engineering Server
Project Details
- Bamimore-Tomi/ghidra_mcp
- Last Updated: 4/13/2025
Recomended MCP Servers
A system monitoring tool that exposes system metrics via the Model Context Protocol (MCP). This tool allows LLMs...
Model Context Protocol server for Replicate's API
An MCP server to help you "play with your documents" via Docling 🐥
A First FIWARE Model Context Protocol Server
MCP Salesforce connector
Model Context Protocol - MCP for Mifos X
Unity Catalog AI Model Context Protocol Server
MCP server retrieving transcripts of YouTube videos