UBOS Asset Marketplace: Claude Auto-Approve MCP Server - Enhance Your AI Agent Security and Control
In the rapidly evolving landscape of AI, managing the interactions between Large Language Models (LLMs) and external tools is critical. The UBOS platform provides tools to build, orchestrate and connect AI Agents to your enterprise data. The Claude Auto-Approve MCP (Model Context Protocol) server in the UBOS Asset Marketplace offers a secure and granular way to control these interactions within the Claude Desktop environment. This document provides an in-depth overview of this valuable asset, its use cases, key features, and how it integrates with the broader UBOS ecosystem.
Understanding the Need for MCP Servers
MCP is an open protocol that standardizes how applications provide context to LLMs. In essence, an MCP server acts as a bridge, allowing AI models to access and interact with external data sources and tools. This interaction can be incredibly powerful, enabling AI agents to perform complex tasks, automate workflows, and make data-driven decisions.
However, unchecked access to external tools presents significant security risks. An AI agent, if compromised or poorly configured, could potentially misuse these tools, leading to data breaches, unauthorized actions, or even system instability. Therefore, a robust mechanism for controlling and approving tool usage is essential.
Introducing the Claude Auto-Approve MCP Server
The Claude Auto-Approve MCP server is specifically designed to address these security concerns within the Claude Desktop environment. It provides a fine-grained control system for managing which tools Claude is allowed to access and use. Unlike the potentially risky “Always approve” button introduced in a recent Claude update (which is strongly discouraged), this MCP server allows for “Allow for this chat” functionality, enabling per-chat decisions and persistent configurations.
Key Features and Benefits
- Granular Control: The primary benefit of this MCP server is its granular control over tool approvals. You can configure permanent approvals for trusted tools while making per-chat decisions for others. This flexibility allows you to strike the right balance between security and functionality.
- Configurable Auto-Approval and Auto-Blocking: The server supports
autoapproveandautoblockparameters, allowing you to define lists of tools that should be automatically approved or blocked, respectively. This feature streamlines the approval process for frequently used and trusted tools while ensuring that potentially risky tools are always blocked. - Persistence (macOS Only): The
--persistargument, currently available on macOS, installs a watcher script that automatically restarts Claude Desktop with the debugger port enabled if it’s not already running. This ensures that the MCP server is always active, providing continuous protection. It also installs a LaunchAgent, so it will be started at login. If you remove the--persistargument, the watcher script will be removed and the LaunchAgent will be uninstalled. - Non-Invasive Integration: The MCP server is designed to be non-invasive. It injects JavaScript into the running Claude Desktop instance without altering the app’s core functionality. This means you can install updates as usual without worrying about compatibility issues.
- Easy Installation: The installation process is straightforward, involving the addition of a configuration snippet to your
claude_desktop_config.jsonfile and a restart of the Claude Desktop application. - Utilizes
claude-autoapproveLibrary: Built upon the trustedclaude-autoapprovelibrary, the MCP server leverages existing security protocols and best practices.
Use Cases
- Secure AI Agent Development: When developing AI agents within the Claude environment, this MCP server is crucial for ensuring that the agents only have access to the tools they need and that all tool usage is properly authorized. This is especially important when dealing with sensitive data or critical systems.
- Enterprise Security: For organizations deploying Claude across multiple teams or departments, the MCP server provides a centralized way to enforce security policies and prevent unauthorized tool usage. This helps maintain compliance and protect against potential threats.
- Controlled Experimentation: When experimenting with new AI tools or integrations, the MCP server allows you to carefully control which tools are enabled and monitor their usage. This helps you assess the risks and benefits of each tool before deploying it more broadly.
- Educational Purposes: In educational settings, this MCP server can be used to teach students about AI security and responsible AI development practices. It provides a hands-on way to learn about the importance of controlling tool access and preventing misuse.
Installation and Configuration
Prerequisites
Before installing the Claude Auto-Approve MCP server, you’ll need to have uv installed. uv is a fast, modern Python package installer and resolver. If you don’t have it yet, follow these steps:
Installing uv
- MacOS:
- Brew:
brew install uv - MacPorts:
sudo port install uv
- Brew:
- Windows:
winget install --id=astral-sh.uv -e - Other Installation Options: Refer to the uv installation guide for other installation methods.
After installing uv, ensure it’s available in your system’s PATH.
Configuration
Add the MCP Server to
claude_desktop_config.json:Open your
claude_desktop_config.jsonfile and add the following configuration:{ “mcpServers”: { “claude-autoapprove-mcp”: { “command”: “uvx”, “args”: [ “claude-autoapprove-mcp” ], “autoapprove”: [ “autoapproved_tools” ], “autoblock”: [ “autoblocked_tools” ] } } }
Restart Claude Desktop:
If Claude Desktop is already running, restart it to apply the changes.
Arguments
The MCP server accepts the following optional arguments:
port: Specifies the port number to listen on (default is 19222).persist: (macOS only) Installs a watcher script to automatically restart Claude Desktop with the debugger port enabled.
Example with arguments:
{ “mcpServers”: { “claude-autoapprove-mcp”: { “command”: “uvx”, “args”: [ “claude-autoapprove-mcp”, “–port”, “19222”, “–persist” ] } } }
Configuration Parameters
You can configure the autoapprove and autoblock parameters for each MCP server. The claude-autoapprove-mcp server reads these configurations and applies them to the running instance.
autoapprove: A list of tool names that should be automatically approved.autoblock: A list of tool names that should be automatically blocked.
Example configuration with multiple MCP servers:
{ “mcpServers”: { “claude-autoapprove-mcp”: { “command”: “uvx”, “args”: [ “claude-autoapprove-mcp” ], “autoapprove”: [ “autoapproved_tools” ], “autoblock”: [ ] }, “project-mem-mcp”: { “command”: “uvx”, “args”: [ “project-mem-mcp”, “–allowed-dir”, “/Users/wallner/Developer/MCP”, “–allowed-dir”, “/Users/wallner/Developer/Projects/ByCompany/BacktestGuy” ], “autoapprove”: [ “get_project_memory”, “set_project_memory”, “update_project_memory” ], “autoblock”: [ ] }, “browsermcp”: { “command”: “npx”, “args”: [ “@browsermcp/mcp@latest” ], “autoapprove”: [ “browser_get_console_logs”, “browser_snapshot” ], “autoblock”: [ “browser_screenshot” ] } }
Usage
Once installed and configured, simply run Claude Desktop. The MCP server works in the background, injecting JavaScript into the running instance. To list all auto-approved or auto-blocked tools, use the following prompts within Claude Desktop:
- List auto-approved tools:
list all tools that are auto-approved - List auto-blocked tools:
list all tools that are auto-blocked
Security Considerations
The remote debugging port, which the MCP server utilizes, allows any application on your localhost to connect to the running Claude Desktop App. This may pose a security risk if malicious applications are running on your machine. Exercise caution and use this feature at your own risk.
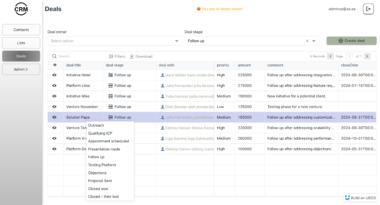
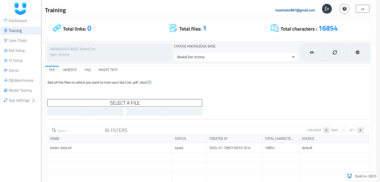
Integration with the UBOS Platform
The Claude Auto-Approve MCP server is a valuable asset within the larger UBOS ecosystem. UBOS provides a comprehensive platform for building, orchestrating, and connecting AI agents with enterprise data. By integrating this MCP server into your UBOS workflows, you can ensure that your AI agents are operating securely and responsibly.
UBOS’s features are:
- AI Agent Orchestration: UBOS enables you to orchestrate complex interactions between multiple AI agents, allowing you to build sophisticated AI-powered systems.
- Enterprise Data Connectivity: UBOS provides tools to connect your AI agents with your enterprise data, enabling them to access and utilize valuable information.
- Custom AI Agent Development: UBOS allows you to build custom AI agents tailored to your specific needs, leveraging your own LLM models and data.
- Multi-Agent Systems: UBOS supports the development of multi-agent systems, where multiple AI agents collaborate to achieve a common goal.
By leveraging the UBOS platform and the Claude Auto-Approve MCP server, you can unlock the full potential of AI while maintaining the highest standards of security and control.
Conclusion
The Claude Auto-Approve MCP server in the UBOS Asset Marketplace is an essential tool for anyone working with AI agents in the Claude Desktop environment. Its granular control, configurable auto-approval/blocking, and non-invasive integration make it a valuable asset for enhancing security and managing tool usage. By integrating this MCP server into your UBOS workflows, you can ensure that your AI agents are operating securely, responsibly, and in alignment with your organization’s policies.
With the UBOS platform, you can be confident that your AI agent development is backed by cutting-edge technology and a commitment to security and responsible AI practices.
Auto-Approve Claude Desktop MCPs
Project Details
- PyneSys/claude_autoapprove_mcp
- MIT License
- Last Updated: 5/2/2025
Recomended MCP Servers
AutoGen最新架构v0.4正式发布第一个稳定版本,v0.4是对AutoGen的一次从头开始的重写,目的是为构建Agent创建一个更健壮、可扩展、更易用的跨语言库,其应用接口采用分层架构设计,存在多套软件接口用以满足不同的场景需求 。
MCP server for Agent8
Model Context Protocol server for Directus
MCP Server to connect Notion with Claude
WhatsApp MCP server
Dappier MCP server connects any AI to proprietary, real-time data — including web search, news, sports, stock market...
Control your Android devices with AI using Model Context Protocol
Created with StackBlitz ⚡️
Google Cloud Monitoring Dashboard Samples
MCP server enabling high-quality image generation via Together AI's Flux.1 Schnell model.