Frequently Asked Questions (FAQ) about the UBOS ATT&CK MCP Server
Q: What is the MITRE ATT&CK framework? A: MITRE ATT&CK (Adversarial Tactics, Techniques, and Common Knowledge) is a curated knowledge base and model for cyber adversary behavior, reflecting the various phases of an adversary’s attack lifecycle and the platforms they are known to target.
Q: What is an MCP Server? A: An MCP (Model Context Protocol) server acts as a bridge, allowing AI models to access and interact with external data sources and tools. In this case, it provides access to the MITRE ATT&CK database.
Q: What tools does the ATT&CK MCP Server provide?
A: The server offers tools to query ATT&CK techniques by ID or name (query_technique), query mitigations for a technique (query_mitigations), query detections for a technique (query_detections), and list all ATT&CK tactics (list_tactics).
Q: How do I install the ATT&CK MCP Server?
A: Clone the repository, install the required dependencies using pip install -r requirements.txt, and configure your MCP client to connect to the server.
Q: What are the deployment options for the server? A: You can deploy the server in local stdio mode (recommended for Smithery/local integration) or in HTTP/SSE mode (for remote access and development).
Q: How do I query a specific ATT&CK technique by ID?
A: Use the query_technique tool with the technique_id argument. For example: {"technique_id": "T1059.001"}
Q: Can I search for techniques by name?
A: Yes, use the query_technique tool with the tech_name argument to perform a fuzzy search by name. For example: {"tech_name": "phishing"}
Q: How do I retrieve the mitigations for a specific technique?
A: Use the query_mitigations tool with the technique_id argument. For example: {"technique_id": "T1059.001"}
Q: How do I retrieve the detection methods for a specific technique?
A: Use the query_detections tool with the technique_id argument. For example: {"technique_id": "T1059.001"}
Q: How do I get a list of all ATT&CK tactics?
A: Use the list_tactics tool with no arguments. For example: {}
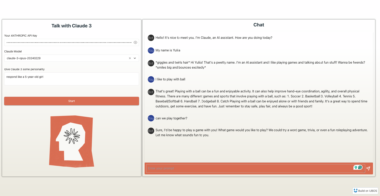
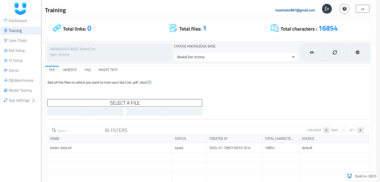
Q: What is UBOS, and how does it relate to the ATT&CK MCP Server? A: UBOS is a full-stack AI Agent Development Platform. The ATT&CK MCP Server is designed to enhance the power of UBOS AI agents. UBOS helps orchestrate AI Agents, connect them with enterprise data, build custom AI Agents with your LLM model, and Multi-Agent Systems. This allows security teams to build more effective automated security workflows and threat detection systems.
Q: Can I use the ATT&CK MCP Server to build custom AI agents for security? A: Yes, the ATT&CK MCP Server is specifically designed to provide AI agents with access to threat intelligence data, enabling them to perform tasks like threat hunting, incident response, and vulnerability management prioritization.
Q: What kind of client is expected to connect to the MCP server? A: Any MCP-compatible client. Smithery and Cursor are specifically called out. Generic HTTP clients will work as well when the server is in HTTP/SSE mode.
attAck MCP Server
Project Details
- alex-llm/attAck-mcp-server
- Last Updated: 5/14/2025
Recomended MCP Servers
这是一个针对于MySQL开发的MCP,该项目旨在帮助用户快速且精确的查询MySQL数据库中的内容
A MCP server for accessing Zoom recordings and transcripts without requiring direct authentication from the end user.
MCP tool for building Android project and feed back error to LLMs.
A task management Model Context Protocol (MCP) server that helps AI assistants break down user requests into manageable...
MCP Crew AI Server is a lightweight Python-based server designed to run, manage and create CrewAI workflows.
小红书MCP服务 x-s x-t js逆向
Universal MCP-Server for your Databases optimized for LLMs and AI-Agents.
This project provides an MCP (Multi-Channel Pipeline) server that acts as a wrapper for the MLB Stats API....
通过 MCP (Model Context Protocol) 提供 A 股市场的行情数据查询功能。