MCP Server on Cloudflare Workers with Bearer Auth
This repository demonstrates a proof of concept implementation of a Model Context Protocol (MCP) server running on Cloudflare Workers with simple bearer token authentication.
Overview
This project shows how to:
- Deploy an MCP server on Cloudflare’s edge network
- Implement basic bearer token authentication
- Create and expose MCP tools via a serverless architecture
Local Development
# Install dependencies
npm install
# Run the server locally
npm run dev
After starting the server, it will be available at http://localhost:8787
Authentication
This implementation uses a simple bearer token authentication scheme. Clients must provide an Authorization header with their requests. The server passes this token to the MCP tools, allowing tools to perform actions based on the authenticated user.
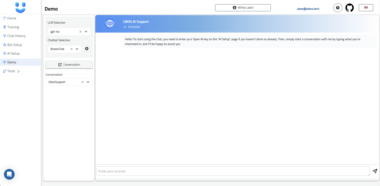
Testing with MCP Inspector
You can use the MCP Inspector to test your MCP server:
Install and start the inspector:
npx @modelcontextprotocol/inspectorConfigure the inspector:
- Switch the Transport Type to
SSE - Enter the URL of your MCP server (local:
http://localhost:8787/sseor deployed:https://your-worker.workers.dev/sse) - Add a bearer token in the Authorization field
- Click “Connect”
- Switch the Transport Type to
Test the functionality:
- Click “List Tools” to see available tools
- Try running the “getToken” tool, which will return your authorization header
- Try the “add” tool with two numbers to test basic functionality


Deploying to Cloudflare
Deploy your MCP server to Cloudflare Workers:
npm run deploy
After deployment, your server will be available at https://your-worker.workers.dev
Project Structure
src/index.ts- Main server implementation with MCP tools definitionsrc/utils.ts- Helper utilities for rendering the web interfacewrangler.jsonc- Cloudflare Workers configuration
Important Notes
This is a proof of concept implementation meant to demonstrate how MCP can run in a serverless environment. In a production setting, you would want to implement:
- More robust authentication (OAuth, token validation, etc.)
- Rate limiting and additional security measures
- Proper error handling and monitoring
Troubleshooting
If you encounter issues:
- Make sure your bearer token is properly formatted in the Authorization header
- Check the worker logs in the Cloudflare dashboard
- Try restarting your local development server
For persistent authentication issues, you may need to clear any cached credentials:
rm -rf ~/.mcp-auth
MCP Server on Cloudflare Workers
Project Details
- Pedropfuenmayor/mcp-cloudflare
- Last Updated: 4/8/2025
Recomended MCP Servers
A Model Context Protocol server implementation for operations on AWS resources
MCP server for analyzing Japanese text with morphological analysis
MCP server that installs MCP Servers
A MCP server for the stock market data API, Alphavantage API.
The OpenAPI-MCP proxy translates OpenAPI specs into MCP tools, enabling AI agents to access external APIs without custom...
Provides integration between the Hunter API and any LLM provider supporting the MCP protocol
An MCP server to interact with Strava